Telemonitoring of Human Biomedical and Biomechanical Signals
Bohdan Shevchuk1, Orest Ivakhiv2,*, Oleg Zastavnyy3 and Mykhaylo Geraimchuk4
1Glushkov Institute of Cybernetics, National Academy of Sciences of Ukraine, 40 Academician Glushkov av., Kyiv 03187, Ukraine
2Lviv Polytecnic National University, 12 Bandera str., Lviv 79013, Ukraine
Western Ukrainian National University, 3 Peremoga Square, Ternopil 46004, Ukraine
National Technical University of Ukraine “Igor Sikorsky Kyiv Polytechnic Institute”, 37 Peremohy av., Kyiv 03056, Ukraine
E-mail: incors@ukr.net; orest.v.ivakhiv@lpnu.ua; olegz80@gmail.com; geraimchuk@kpi.ua
Corresponding Author
Received 24 January 2022; Accepted 18 July 2022; Publication 15 February 2023
Abstract
Methodological and algorithmic bases of the local-regional and global wireless networks operation for functional states of people long-term monitoring are offered. The construction of efficient wireless networks and portable devices for monitoring biological objects is proposed. High-speed algorithms for processing, encoding, encrypting and transmitting samples of monitoring signals and video data frames using a signaling approach are proposed. The express analysis of monitoring signal samples is offered. The described methods of effective long-term monitoring of functional states of biological objects using wireless networks, algorithms of operational processing, coding, encryption and express analysis of signals are the basis of information technology of wide application. The technology is focused on evidence-based monitoring of the condition of operators of various human-machine complexes, systems, vehicles, aviation and space systems, monitoring of athletes and healthy people in order to prevent various diseases.
Keywords: Wireless monitoring networks, object systems, processing algorithms, signal sample encoding, data compression and protection, express signal analysis, transmission of high-capacity information packets.
1 Introduction
The high pace of modern life, competition between countries for markets, accidents in industry, energy, transport, aviation, competition in sports show that an important factor of the effective society creation is the human factor.
With the advent of the element base of cheap, small and energy-efficient sensors, processors and radio modules on the market, wireless Holter (multi-day) ECG monitoring has become widespread [1]. Trackers [2], smart T-shirts [3] and sneakers [4] have become widespread in the sport medicine and sport as well. Specialized devices and medical smart watches are being developed [5] as well as there is proposed the construction of systems of long-term monitoring of the functional state [6, 7].
At this stage of the remote monitoring systems development for a large number of people there is no comprehensive information technology for portable network intelligent devices building for the rapid analysis of monitoring biomedical and biomechanical signals, the prompt determination of the most informative samples and transmission to remote databases and experts monitoring of the people condition in various fields of their activities.
With the development of microcomputers and radio modules, wireless means of transmitting information over long distances, conditions are provided for the implementation of remote monitoring of working and functional states of many controlled persons.
The aim of the article is to develop methodological and algorithmic bases for the local-regional and global wireless monitoring networks operation, as well as wearable devices for daily (or multi-day) monitoring of functional states of objects (bio objects) of long-term long-term monitoring.
2 Efficient Wireless Networks for Long-term Bio-objects State Monitoring Creation
Observing of various monitoring objects (MO) as the subject to control is carried out by installing portable devices on them, which are the primary link of local-regional and global wireless networks. Such devices are operating systems that can be subscriber systems of wireless networks, including [8–10]:
(1) local-regional sensor networks (for example, cellular Zig-Bee networks);
(2) mesh-networks with routers for the resources to Internet access (Wi-Fi-networks);
(3) mobile and IoT networks (use of 3–5 G radio modules and IoT mobile network radio modules);
(4) microsatellite and satellite (terrestrial space) networks.
Modern wireless networks (WN) are developing in the direction of cellular and cluster networks with self-organization of data packet transmission between remote subscribers. The operation of multi-cell monitoring WN is based on the operation of the cell that provides the transmission of information packets (IP) with a topology of communication “one to one”, while the transfer of information from one subscriber system to another can be carried out on different routes.
An effective way to transmit monitoring data from the object system (OS) is to use the short-range radios based on sensor networks (WN) (e.g., ZigBee [9, 10]), IoT networks [11–15] and the standard long-range radios (Wi – Fi, Ethernet, Internet), united in a single network. Narrowband antenna systems are used for transmission over relatively long distances (tens of kilometers), which are installed at the priority heights. The operation of sensor networks is based on the interaction of neighboring portable subscriber systems (SS), built on the IEEE 802.15.4 standard with the ZigBee stack.
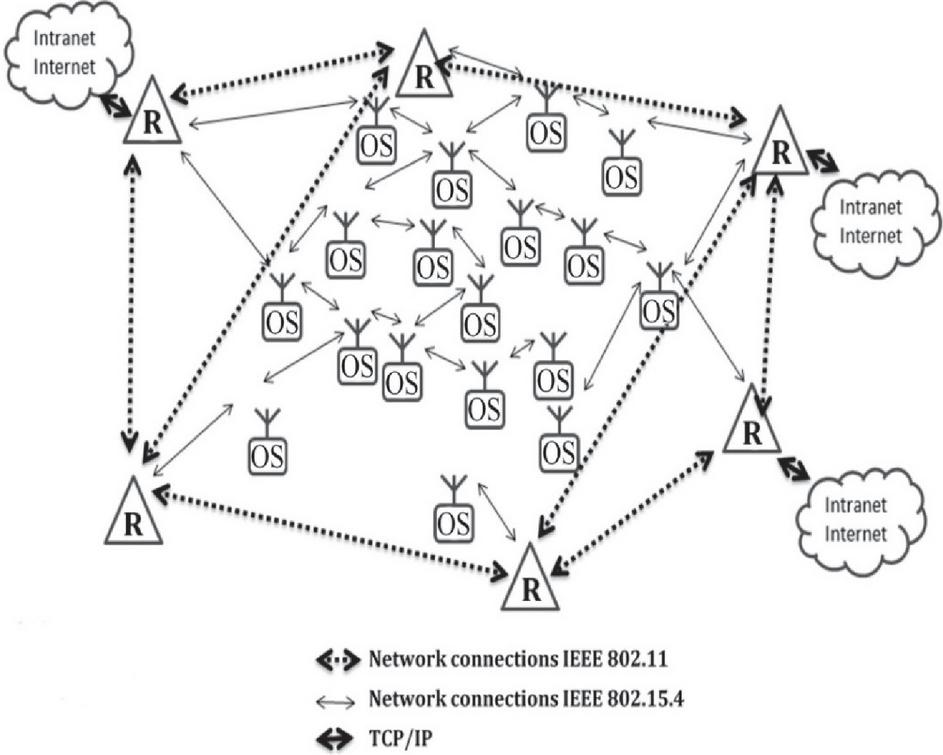
The most effective way to implement communication between the SSs is the deployment of a branched local and regional radio network in the relevant area (Figure 1). At the lower level, the basis of the local radio network is formed by cellular sensor networks, which cover the portable OS of sensor networks. The transmission of information is carried out in the network “from neighbor to neighbor”, and each subscriber of the cell WN has a connection with the appropriate number of neighboring operating systems. This is how the conditions for the formation of alternative ways of packet transmission are provided. Remote operating systems can be connected to one of the operating systems of sensor networks using a more powerful radio transmitter and a specialized antenna system (with high-altitude antenna or narrow-beam antenna). Routers (R) of sensor networks with autonomous and/or stationary power supply relay information packets to the general-purpose network.
Figure 1 The structure of the local-regional radio network for the organization of data transmission between the SSs of WN.
Monitoring signals and MO indicators are input (selected) using digital sensors, analog sensors, video modules. Monitoring of the MO functional states involves the implementation of network flows at the point of origin, i.e., on the objects of monitoring, a set of long-term measurement and computational operations for selection and transmission to remote databases, cloud environments of the most informative, accurate and reliable long-term monitoring data [16, 17]. The structure of a set of algorithms for operational filtering, processing, encoding and transmission of protected monitoring data using WN was described in detail previously [16]. The processed and encrypted data must be crypto protected, i.e., protected from their substitution and access to unauthorized subscribers and WN users. Accordingly, high-performance OS processors, which are WN subscribers, are installed on the MO. Such object systems operate under many constraints, including limitations on power consumption, CPU performance, radio power, weight, and dimensions of object devices and systems.
Depending on the type of wireless network (sensor network, mobile network, IoT network, etc.), problem orientation in the OS used single radio modules or combinations of different radio modules of the WN (Bluetooth, ZigBee, 6LoWPAN, etc.), Wi-Fi, GSM, CDMA. Promising is the use of radio modules of wireless IoT networks, including LTE NB-IoT, LoRaWAN, information-efficient radio modules of the ISM-frequency band with the transmission of packets with increased information capacity [16]. For reliable and secure transmission of the monitoring data, it is advisable to use the main and backup radio paths, the organization of data transmission packets in the noise of the radio channel. To select monitoring signals from different parts of the human body, it is advisable to organize the operation of a specialized radio network (nano cell) at the body where sensors and other devices are subscribers of the radio network, and the OS is both the central station (CS) and repeater.
Thus, a promising way of long-term monitoring of persons as subject to long-term remote control is the use of wearable OS sensor networks, which are subscribers of the local and regional radio network. At the same time, the most informative and suspicious fragments of the ECG are transmitted to the central database (i.e., cardiologists) with minimal delays by operative detection of areas with characteristic features, and daily monitoring data are recorded in the OS flash memory.
3 Processing, Coding, Encryption and Transmission of Monitoring Signal Samples Algorithms
Monitoring signals, measured values and indicators are the primary information images of the current functional states of the OM. They are complemented by video frames or short videos (sequences of video frames) of current and working situations, as well as measuring video frames and videos of appropriate quality. When entering signals, the sampling frequency is chosen to be unprofitable and significantly depends on the metrological requirements and the maximum signal frequency . The optimal input of signals is the selection of samples with the adaptive coding period [15] as follows
| (1) |
where is the indicator of the input signal-to-noise ratio, which corresponds to the difference between the values of input samples with noise and filtered , is the current increment of the filtered signal.
Effective methods and algorithms of efficient (the fast and accurate) compact coding of signals and video signals are based on the signaling approach [16, 18]. The essence of coding is that, considering the specifics of the use of adaptive algorithms for compressing signals and video signals with a minimum number of computational operations and with allowable loss of information to implement the definition and compact coding/decoding of the essential samples/pixels (ES/EP). These include extremums (E), minima (M) and inflection points (IFL) of the envelope signals (video signals). As for the samples of the envelope video signals, i.e., pixels, they are obtained from rows or columns of R-, G-, B- frames of video data, which are transmitted from video modules to the processor module of the OS of the WN. The definition of the ES/EP allows to minimize incoming information flows without losing the quality of monitoring data, i.e., having the parameters of ES/EP nonlinear algorithms (splines) restore intermediate samples (pixels). To further minimize the flow in many cases, the envelope signals and video signals can be smoothed and among the pre-defined ES/EP stand out significant samples (pixels) that do not visually distort the envelope. It should be noted that the basis of high-quality compression and recovery of envelope signals and video signals is accurate coding and restoration of amplitude-time or number parameters of ES/EP considering the requirements and features of applied tasks. This approach is the basis for substantiating the compression limit of signals and video signals with information loss. After adaptive filtering [18] in the process of operative processing and coding of signals (video signals) extremes and minima are determined based on analysis of signs of difference values . Inflection points are the second derivative of the envelopes, which are temporal functions. Increments are calculated to quickly determine the inflection points on the dynamic sections of the signals.
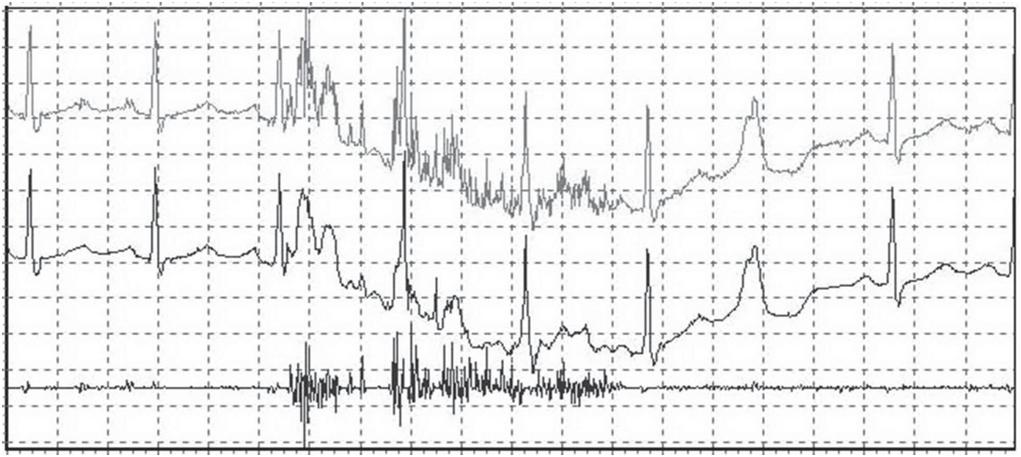
In real conditions of long-term monitoring of the state of objects, as a rule, in the long samples of signals there are areas of signals free from noise and areas with noise. After filtering, we obtain the resulting signal, which in areas with noise is unreliable. Therefore, considering the possible interference with the input signals, it is important to pre-control the reliability of the entered samples of signals. Consider areas of the ECG obtained in the process of Holter (daily) monitoring of the cardiovascular system of the human body (Figure 2) [16].
This figure shows the ECG with noise (curve 1) and after filtering (Figure 2, curve 2), in certain areas of which (in areas of the input signal with noise) there are distortions. It is possible to quickly determine such distortions of the encircled filtered signal based on the analysis of the difference signal (Figure 2, curve 3), which, in practice, characterizes the level of input noise. After filtering the signal and determining the essential samples parameters in their vicinity, the difference values are calculated, which are used in the process of compressed coding of the essential sample parameters of the filtered signals (Figure 2, curve 2). For simplicity of coding, considering the peculiarities of applied research, it is advisable to determine and encode noise-free (reliable) and noise-distorted (less reliable) areas of signals.
Figure 2 The results of daily monitoring of human ECG fragments (1 – the input ECG with the noise; 2 – the filtered ECG; 3 – the noise component of the ECG [16]).
The fragments of daily ECG monitoring (Figure 2) show the most informative sequences of cardio cycles, where normal cardio cycles are observed at the beginning, followed by extrasystoles (the most informative areas of daily ECG monitoring), followed by normal cardio cycles. These fragments of the daily ECG monitoring should be promptly detected by CPU means of the OS of the WN (practically determined in the rate of monitoring data entry) and transferred to a remote database, as well as remote experts (cardiologists). This approach to human cardio monitoring differs favorably from traditional Holter monitoring (the delayed monitoring).
Thus, in the process of inputting data from the OM processor means of the WN operating system, it is important to control the conditions of signal input and the degree of their distortion by noise and interference. After filtering and compressing signals with losses in the service information, data of adaptation and optimization of input data processing are recorded [16], including amplitude-time parameters of the essential samples areas of noise-free signals essential sample parameters are coded more accurately) and the essential samples areas of signals with noise (coded less exactly).
After compression of signals and video signals with controlled loss of the information in the original data set, as a rule, there is redundant data. Therefore, for further data compression, it is advisable to implement operational algorithms for compact coding of lossless binaries. Effective operational compression of the lossless data compression should be performed in two stages: the compression of data arrays with the most common binary sequences and the compression of pseudo-chaotic binary sequences, for example, based on a dictionary approach [16]. In both cases, when there is time for data encoding, to increase the compression ratio, data is compressed sequentially or in parallel for different input n-bit sequences and after determining the minimum output data array, a decision is made to select optimal encoding parameters recorded in the service data.
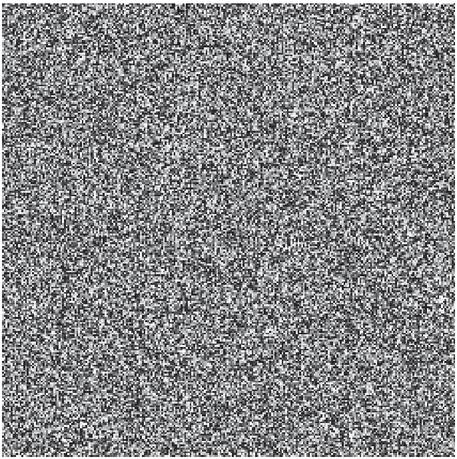
After data compression, it is expedient to quickly protect (encrypt) arrays of bit sequences based on the gamification of data of a certain length (often variable) with the corresponding cryptocurrency sequences, which are variable for each portion of data. As example, it is shown (Figure 3) the chaos gram of a crypto-stable long-term pseudo-random sequence (PRS) [16]. The chaos gram reflects the dependence of the current n-bit sequence (n 8) on the next one. That is, one sees that there are no dependencies, the generated array is almost uniformly distributed or pseudo-chaotic. It should be noted that qualitatively compressed data sets are practically also pseudo-chaotic data.
Figure 3 The chaosgram of the long-term crypto – stable PRS [16].
Crypto – stable PRSes act as disposable ciphers. After encrypting the data, it is obtained a crypto array as follows
| (2) |
where n is the maximum number of bits of the array, for which is valid the following expression
| (3) |
where is the sequence of bits of the compressed data array, is the sequence of random bits, the values of which depend on the following current secret key
| (4) |
To recover data to the corresponding subscribers of WN (for example, the subscriber-receiver of the crypto-stable IP) it is necessary to know the code keys to generate the relevant fragments of crypto- stable PRS.
To protect the monitoring data with a high degree of the information protection, it is advisable to repeatedly gamification of the compressed data sets with crypto-stable PRS in the lossless data compression process, the implementation of the operational noise-resistant coding and before the operation of forming code-signal sequences of information packets with the high information capacity [16, 18]. Additional protection of the information is the mixing of data frames of a group of neighboring packets, the algorithms of which are known only to two subscribers who carry out the current transmission of encrypted IP. As a result of complex compression-protection of monitoring data arrays, protected (crypto-stable and noise-resistant) data are formed in the form of pseudo-chaotic data. It does not matter what the input data is, i.e., whether it is a sample of measurement signals, arrays of measured values or video data frames. Rules and selected parameters of data coding, rules of generation of crypto-stable PRS should be known only to the transmitter and receiver of the current IP. Delivery and protection of this information is achieved in various ways, including the use of high-speed asymmetric cryptography algorithms, by transmitting noise-like packets of information in radio channels with interference and using subscribers of directional antennas [16]. As a rule, the data set that defines the current rules of the coding, encryption and transmission of the monitoring data should be a cryptographic array of information owned by the above two subscribers. WN intermediate subscribers, which are packet repeaters together with the transmitter and receiver of the IP, have the current session keys.
The basis of covert and reliable transmission of IP in the noise of the radio channel is the implementation of a pair of subscribers “sender-receiver IP” known only to them methods of encoding primary data and generating noise-like interval pulse signals adapted to the noise level in the communication channel. To implement the hidden transmission of information in the noise of the radio channel needs [8] support of pairs of subscribers of the minimum required energy ratio signal/noise in the radio channel.
When using standard WN and protocols (Bluetooth, ZigBee, 6LoWPAN, Wi-Fi, GSM, CDMA, etc.) data protection is carried out at the information level of the OS. In information-effective monitoring WN [16] the additional data protection is carried out at the level of formation and transfer of the code-signal sequences (CSS) of the IP.
Construction of the information and energy-efficient WN is based on the implementation of network subscribers optimized for speed and accuracy of coding methods and algorithms of the compact, crypto-stable, and noise-resistant data coding with the prompt adaptation of channel signals to the current noise level in the radio channel. Crypto-stable data coding by means of the OS is carried out in the data compression process and in the formation of the source information packets in the forming the CSS of the IP process. The code keys for generating of the crypto-stable pseudo-random sequences used in the encoding data process by the method of a single notebook, as well as codes for forming the CSS of the current packets are known only to the transmitting subscriber and the receiving subscriber of the IPs. Due to the minimization of the output streams of the information packets, the packet transmission in the noise of the radio channel, such radio networks are highly competitive to solve the problem of the long-term monitoring of the various objects state. In addition to sensory and local radio networks, the proposed set of algorithms can be successfully used in the construction of wireless pico – networks on the human body to transmit monitoring signals from different parts of the body to the OS – packets repeater (arms, legs, the head, etc.).
Thus, the effective implementation of secure and hidden transmission of the information in the monitoring radio networks is achieved by building of the information-efficient operating systems, processors which in the data entry sites (measuring signals, images, data sets) provide a set of complementary methods and algorithms for compact coding and crypto-stable, noise-resistant data coding, forming a CSS with a base that provides the minimum required signal-to-noise energy ratio in the radio channel. Depending on the tasks of the object long-term monitoring, considering the available time to perform a set of algorithms for data compression without loss and gamification of the data with crypto-stable PRS, the minimization and the reliable information flows protection are achieved by the OS in the network data streams origin. The novelty of the approach to compression and data protection by performance-limited means of WN is to minimize the computational operations in the process of generating compressed and secure streams of monitoring data with the hidden information addition for the effective crypto security and recovery of distorted channel interference. By minimizing the input monitoring data streams, the data packets flow is minimized by each WN operating system.
4 Monitoring Signal Express Analysis Algorithms
To quickly identify and prioritize the transmission of the most informative fragments and areas in the monitoring signal samples, the ES informativeness indicators are calculated [16]. This approach is the basis for the most characteristic complexes and informative areas of signals identifying.
In places where network flows are formed, it is important to determine the data to be transmitted. It is important to organize the transfer of monitoring data by means of the WN OS, depending on the MO state. To identify the current IS in the process of input and pre-processing signals, it is advisable to control the presence of signals within the allowable minimum and maximum amplitude values as well as the stationarity conditions of information selection when the MO is in the different functional states and operating modes, and indirectly or directly determine the current signal-to-noise ratio in the input signals [16]. It is necessary to realize the express analysis of the entered and filtered data directly on MO by the processor means of the WN OS. Based on the control over changes in the most informative signal parameters (amplitude values, time intervals, frequency parameters, increments) and calculated the statistical, correlation, spectral, entropic, chaotic, etc. values and functions is achieved by identifying the most informative monitoring data that characterize the behavior of the MO. In essence, the OS simulates the monitoring object state by identifying the most informative data and transmitting a set of informative and reliable data to the remote powerful computers, which provide a basis for refining and obtaining highly informative models of the MO operation, determining, and correcting their states. At the CS of the WN request the OS can additionally transmit compressed arrays of the primary data, which are analyzed and processed by the powerful algorithms. The proposed approach to the monitoring significantly facility increases the effectiveness of evidence-based monitoring of many MOs distributed over the large areas. The results of this approach provide prompt determination of the current MO state, which is confirmed by reliable monitoring data (signal samples, the most informative segments and areas of signals, video frames) and the results of in-depth modelling and analysis by the supercomputer.
The essence of modelling and determining the states of the MO is as follows. Monitoring signals and video data are the primary informational images of the behavior of objects and subjects, their current functional and operational states. It is important that these signals and video data are informative, i.e., for example, that changes in the state of objects are to some extent accompanied by changes in the amplitude-time parameters of signals and video signals. These may be obvious local changes in the envelope signals and video signals in the certain envelope areas. Also, with a certain period or chaotically, characteristic fragments of signals and video signals may appear, typical areas of the monitoring signal samples may change periodically. Accordingly, the change of the MO states is transformed (to a greater or lesser extent) into a change in the signal and video signal parameters. Based on the detection and analysis of changes in the primary and secondary characteristics of monitoring signals, analysis of the relevant fragments of video frames and areas of video signals, operational monitoring of the MO states in the input of monitoring data places is carried out.
Considering the minimization of calculations by the limited performance of the OS, the operational modelling and determination of the MO information states is achieved based on aperture and / or zone control of changes in the relevant (selected) indicators and calculated signal characteristics in accordance with the following expressions:
| (5) |
where – is the value of the -th Boolean element of the vector – of the information state (IS) of the MO in the aperture or band control process of the relevant parameters and values of the -th signal; – is the variable to be controlled; , – is the maximum number of monitoring signals; , – is the maximum number of the signal samples of the -th signal; – is the reference indicator value (the conditional current rate) of the -th signal or the calculated value of the -th information state of the MO is the number of ISs and – their maximum number; – is the aperture value; – is the value of the Boolean element of the MO IS – vector; – is the function of the monitoring signal to be calculated.
The monitoring signals indicators that can be monitored over the duration of the signal sample are as follows: the amplitude, frequency and time characteristics of typical fragments and areas of signals; the assessment of the current steepness of the signal; estimation of the average steepness of the signal on selected segments and intervals; the estimation of signal steepness between the adjacent significant (the most informative) samples of signal sampling. It should be noted that the current sample of monitoring signals and their individual fragments (the various periodic sequences) are sufficiently informative to characterize the ES parameters, which are the extremes and inflection curve points (points of the motion change). To identify informative signal complexes at a given interval , informative characteristics are calculated as follows
| (6) | |
| (7) |
where – is the absolute difference between the current neighboring signal extremes, – is the number of signal samples and – is the number of the ESs per interval .
Additional arrays of difference amplitude and time values are formed for the operative analysis of periodic signals from the sequence of amplitude-time parameters of the ES. Having the current (the -th) and next (the -th) values of the corresponding data set or vice versa on the planes with Y – X coordinates for each of the arrays of the corresponding ESs are formed areas of the grouping points that fall into the corresponding squares (areas) of the Y – X plane. Each square of the Y – X plane is numbered. Based on the calculation of the number of hits in the respective squares of the points with the -th and the -th coordinates of the ES of the relevant data set, diagrams are determined and formed, which characterize the information state of the monitored object. It is possible to construct multidimensional (XYZ) planes of the grouping of the proper corresponding points. By the operative deviations control of the signal sample envelope characteristics (the spectra, correlation functions, entropies, distribution functions of calculated values, histograms, etc.) and the signal envelope differential characteristics (histograms of the corresponding signal fragment frequencies, the amplitude, and other changes) in the relation to reference values are formed the logic function vectors that in a compact form describe the MO state and minimize the flow of primary data transmitted in radio channels.
Thus, the amplitude-time parameters of the ES are the basis for the operational correlation, spectral entropy and chaotic parameters of signals calculating, and various arrays of the ES difference data can be used to calculate and display two-dimensional and multidimensional chaotic parameters and various histograms. The minimum duration of monitoring data sampling depends on the monitoring tasks and the need to calculate certain (the amplitude-time, frequency, spectral, correlation, entropy, chaotic, etc.) characteristics of signals and significantly depends on the minimum informative frequency and the period of recurrence of periodic signals . For example, to calculate the periodic signal amplitude-time parameters, it is sufficient to accumulate a sample of data lasting 3-5 signal periods, and to calculate correlation and spectral characteristics, the accumulation interval corresponds to the analysis interval .
Displaying the results of operational calculation and analysis of the spectral, correlation and chaotic functions and parameters estimates can be used to show the status of monitoring objects at the places of input, coding, and data collection.
Thus, to implement the effective long-term monitoring of the object state after input and filtering signals, the amplitude-time parameters of significant samples of the envelope signals are determined, which are the basis for forming the compact and reliable monitoring data sets. ES parameters are input data for the operational calculation of the spectral, correlation, entropy, and chaotic data directly in the places of input and formation of the network data flows. The aperture and band analysis of the calculated parameters, values, and functions in the places of information flows in the monitoring WN provides minimization of data to be transmitted and relayed over long distances, as well as prompt display of the results of rapid analysis of the sensor network portable OS.
5 Conclusions
Effective monitoring of many people is achieved by installing a variety of wireless portable information and energy-efficient object systems at the monitoring site. The basis of long-term monitoring of functional states of individuals is daily and multi-day selection and analysis of biomedical and biomechanical signals, output data of sensors and video modules to identify the most informative areas of monitoring signals and measured and calculated values. The algorithmic basis for the effective operation of object system monitoring networks is the implementation by object processors a set of complementary adaptive algorithms for processing, compression-protection of monitoring signals and images, arrays of measured values, formation and transmission of short packets of pseudo-chaotic and protected data. For accurate coding and retrieval of monitoring signal samples, video data frames with a minimum number of computational operations, preference should be given to the signal approach, according to which it is important to detect, accurately and compactly encode, encrypt, transmit and restore parameters of the most informative and reliable samples. extremums and inflection points of bypass signals and video signals. In the process of filtering by object system processors, it is important to classify and compactly encode areas and fragments of signals that are free of noise and affected by noise. To optimize the transmission of large amounts of monitoring data in radio networks, it is advisable to quickly determine the object processors of monitoring object information states based on rapid analysis of filtered signals and calculated functions and quantities, including correlations, spectra, entropy and chaotic indicators. To select monitoring data from different parts of the body, it is advisable to use pico-radio networks with information-efficient data transmission from sensors and video modules with the involvement of object system repeaters.
References
[1] A. Melnyk, Y. Morozov, B. Havano, P. Hupalo ‘Health Supervisor: Mobile Application for Round-the-Clock Remote Monitoring of the Human Functional State,’ The 2nd International Workshop on Intelligent Information Technologies & Systems of Information Security (IntelITSIS-2021). CEUR-WS, Vol-2853, pp. 24–37, 2021.
[2] ‘8 Tracking Gadgets to Never Losing Your Belongings – Hongkiat,’ [Online]. Available: https://www.hongkiat.com/blog/tracker-gadgets-never-lose-belongings/. [Accessed 16 06 2022].
[3] ‘STAT Sports | APEX Athlete Series |GPS Performance Tracker,’ [Online]. Available: https://statsports.com/. [Accessed 16 06 2022].
[4] ‘Sneakers_Are smart sneakers the next big thing,’ [Online]. Available: https://www.the-spin-off.com/news/stories/Sneakers-Are-smart-sneakers-the-next-big-thing-14519. [Accessed 16 06 2022].
[5] ‘Best medical alert smartwatches of 2022_TechRadar,’ [Online]. Available: https://www.techradar.com/best/best-medical-alert-smartwatches. [Accessed 16 06 2022].
[6] Gaoce Han, Jize Yan, Zhen Guo, David Greenwood, James Marco, Yifei Yu, ‘A review on various optical fiber sensing methods for batteries,’ Renewable and Sustainable Energy Reviews, Volume 150, 2021, 111514, ISSN 1364-0321, https://doi.org/10.1016/j.rser.2021.111514. (https://www.sciencedirect.com/science/article/pii/S1364032121007930).
[7] Karl E.Friedl, ‘Military applications of soldier physiological monitoring,’ Journal of Science and Medicine in Sport, Volume 21, Issue 11, November 2018, Pages 1147–1153, https://doi.org/10.1016/j.jsams.2018.06.004.
[8] B. Sklyar, ‘Digital Communication. Theoretical Foundations and Practical Application’, 2nd ed.: Moscow: Williams Publishing House, 2003.
[9] Z. Shelby, C. Bormann, ‘6LoWPAN: The Wireless Embedded Internet’, WILEY, 2009.
[10] W. Dargie, C. Poellabauer, ‘Fundamentals of wireless sensor networks: theory and practice’, John Wiley and Sons, 2010.
[11] Gartner, The Internet of Things, Report, accessed on 17 November 2015 from http://www.gartner.com/technology/research/internet-of-things.
[12] M. Chiang and T. Zhang, ‘Fog and IoT: An Overview of Research Opportunities’, in IEEE Internet of Things Journal, vol. 3, no. 6, pp. 854–864, Dec. 2016.
[13] S. A. Hinai, A. V. Singh. ‘Internet of things: Architecture, security challenges and solutions’, 2017 International Conference on Infocom Technologies and Unmanned Systems (Trends and Future Directions) (ICTUS), pp. 1–4, Dubai, 2017.
[14] Z.-K. Zhang, M. C. Y. Cho, and S. Shieh, ‘Emerging Security Threats and Countermeasures in IoT’, Proceedings of the 10th ACM Symposium on Information, Computer and Communications Security-ASIA CCS ’15, 2015, pp. 1–6.
[15] Y. Kondratenko, et al., ‘Inspection mobile robot’s control system with remote IoT-based data transmission’, Journal of Mobile Multimedia, Vol. 17, Is. 4. pp. 499–522, 2021. DOI: 10.13052/jmm1550-4646.1742.
[16] B. M. Shevchuk, ‘Methods and algorithms for improving the information efficiency of wireless monitoring networks’, Kyiv: Naukova Dumka. 2020.
[17] Y.P. Kondratenko, et al., ‘Advanced Control Systems: Theory and Applications’, Series in Automation, Control and Robotics, River Publishers, Gilstrap, Delft, 2021.
[18] B. Shevchuk, M. Geraimchuk, O. Ivakhiv, Yu. Brayko, ‘Highly Information and Energy-efficient Monitoring Data Transmission in IoT Networks’, Journal of Mobile Multimedia, Vol. 17, Iss. 4, pp. 465–498, 2021. DOI: 10.13052/jmm1550-4646.174.
Biographies

Bohdan Shevchuk graduated in 1978 from the Radio Engineering Faculty of the Lviv Polytechnic Institute in the radio engineering and during 4 years worked at the Lviv Research Radio Engineering Institute as a radio engineer. In 1984 he entered and in 1987 graduated as PhD from the Institute of Cybernetics named after V.M. Glushkov National Academy of Sciences of Ukraine. Since 2018 he received Doctor of Technical Sciences degree. Now he works with the department of the numerical methods optimization in the Institute of Cybernetics as a leading researcher, specializing in processing, encoding, encryption and transmission of signals and images, construction of monitoring information-efficient radio networks, including sensor, local-regional, micro-satellite networks. and Internet of Things. He has more than 160 scientific works, including 4 monographs, 7 copyright certificates and 2 patents of Ukraine for inventions.
Further theoretical and practical developments of the author are aimed at building secure (crypto-resistant and noise-resistant) high-speed radio networks for various purposes, operating in many constraints, data compression, transmission of highly informative and pseudo-chaotic information packets, creation and implementation of experimental wireless telemedicine networks and networks. industrial monitoring, ecomonitoring, security networks, object and on-board means and wireless intelligent sensors, energy efficient intelligent video modules.

Orest Ivakhiv is from Lviv, Ukraine. Professor O.Ivakhiv received his M.A. Sc. in Electrical Engineering from The Lviv Technical University (Ukraine), the Ph.D. in Communications from The Moscow Aviation Institute (Russia), the Sc. D. in Electrical Instrumentation from Lviv Polytechnic National University (Ukraine). Orest Ivakhiv was a visiting professor at the Department of Electrical and Computer Engineering at The University of Toronto (Ontario, Canada) in 1994. Since 1968 professor O. Ivakhiv is a faculty member at the Computer Technology, Automation and Metrology Institute of Lviv Polytechnic National University. Now Orest Ivakhiv is a Head of the Intelligent Mechatronics and Robotics Department. Orest Ivakhiv has more than 300 publications, 12 patents. His research interests include electrical measurement and instrumentation, informative measurement theory, adaptive data processing, data compression, enumerative coding, communication theory and mechatronics.

Oleg Zastavnyy graduated from the Ternopil National Economic University (Ternopil, Ukraine) in 2002 with a degree of systems-engineer majoring in the computer systems and networks. In 2007 he defended the Ph.D. Thesis on specialty 05.13.05 – elements and devices of computers and control systems in the Ternopil National Economic University (Ternopil, Ukraine). Topic of work: “Methods of constructions of the special processors and analog-digital coders in the Galois base”. During 2008 – 2010 he was employed as the Head of the Department of Software and Computer Systems at the Halician Institute. V. Chornovola and in 2010 – 2011 as the Head of the Department of Natural, Mathematical and Computer Disciplines at the Halician Institute by V. Chornovola name. From 2011 till nowadays he is a faculty of the Department of Specialized Computing Systems at Western Ukrainian National University (Ternopil, Ukraine).

Mykhaylo Geraimchuk, Doctor of Technical Sciences, professor of the Instrument Making Department of the National Technical University of Ukraine “Ihor Sikorsky Kyiv Polytechnic Institute”, Kyiv, Ukraine. He graduated from the Kyiv Polytechnic Institute in 1974, the Department of Precision Mechanics, where he has worked since 1974. From 1988 to 2001 he was the Deputy Dean of the Instrument-Making Faculty, from 2001 to 2019 he was the Head of the Instrument-Making Department, and now he works as a Professor at this Department. Received more than 15 patents. He has more than 150 scientific works, including more than 10 monographs and books, more than 30 publications indexed in international Scopus databases, more than 11 textbooks and guidelines. He has collaborated with China, Algeria, France and other countries. He has scientific interests in the fields of instrument making, artificial intelligence, sensor networks; inertial sensors, mechatronics and robotics, unman vehicles and also participates in projects on psychology of creativity, computer programs of training and stimulation of genius and others.
Journal of Mobile Multimedia, Vol. 19_3, 877–896.
doi: 10.13052/jmm1550-4646.19310
© 2023 River Publishers