Smart Attendance Monitoring System with Computer Vision Using IOT
Ashwin Raj, Aparna Raj and Imteyaz Ahmad*
ECE Department BIT Sindri, Dhanbad, Jharkhand, India
E-mail: rajashwin167@gmail.com; aparnaraj286@gmail.com; iahmad@bitsindri.ac.in
*Corresponding Author
Received 30 September 2020; Accepted 30 November 2020; Publication 26 January 2021
Abstract
The main aim of this project is to create a smart attendance monitoring system which will use the concept of face recognition to identify students. On the basis of this a database will be created containing the information of attendance date wise. Apart from reducing time it will also help in replacing the laborious conventional method of using logbooks. The system also has the feature to send emails to the administrator about the student ‘s attendance status at the time of recognition itself. At the time of closing of the camera absentees’ names will be called out.
Keywords: Feature extraction, HOG algorithm, SQLite.
1 Introduction
Attendances of every student are being maintained by every school, college and university. Empirical evidences have shown that there is a significant correlation between students who have poor attendances and their academic performances. There was also a claim stated that the students who have poor attendance records will generally link to poor retention. Therefore, faculty has to maintain proper record for the attendance. The conventional methods practiced in most of the institution includes manual entering of attendance in logbooks which is time consuming and can be easily manipulated. Calculating the average attendance of each student is also laborious. Bunking the classes or giving proxies for the absentees has also become quite flexible. Hence to solve all these problems we are introducing the idea of automated attendance monitoring system which works on the concept of face recognition.
The main motivation for the project was the slow and inefficient traditional manual attendance system. So, why not make if automated fast and much efficient. Also, such face detection techniques are in use by the department of a criminal investigation where the usage of CCTV footages and detecting the feces from the crime scene and comparing them with criminal database to recognize them. It is also becoming as a feature of daily life in China, where authorities are using it on the streets, in subway stations, and at airports. The proposed model is based on face recognition mechanism. Whenever a student enters the class and comes across the camera module of the system his image is captured in the system and is recognized and validated if he/she is a student of the class. If recognized then his attendance is automatically marked via post processing of the system.
2 Methodology
The concept is based on face recognition technique that requires the modules according our need. The system in which the software runs needs a web cam and internet connection. The camera starts to capture video and starts recognizing and marks the student’s attendance. The attendance database is saved on the system and also send to the user via cloud services through email which can be accessed for later verification purpose. The system architecture consists of various stages and steps ranging between creating dataset and updating of the database [1–3].
HOG Algorithm for Face Detection:
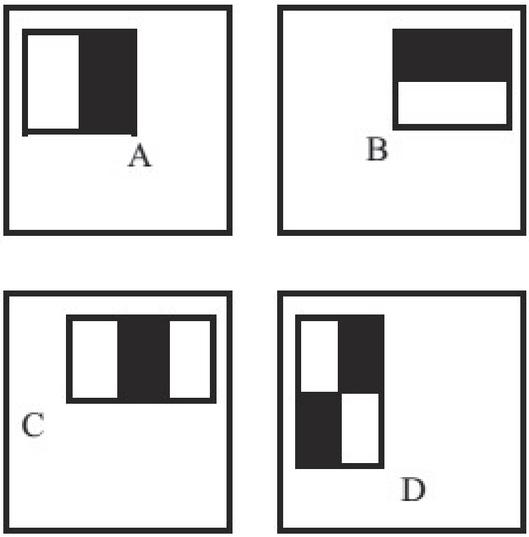
A HOG is a feature descriptor generally used for object detection. In the current example, all the face sample images of a person are fed to the feature descriptor extraction algorithm; i.e., a HOG. The descriptors are gradient vectors generated per pixel of the image. Histograms of Oriented Gradients Histograms of oriented gradients (HOG) finds applications in object and pattern recognition domain as it is capable of extracting crucial information even from the images that are obtained under garbled environments [2, 4–6]. It is therefore well suited for tackling the facial recognition problem. The feature extraction process of HOG is based on extracting information about the edges in local regions of a target image. Simply put, HOG feature extraction is primarily the characterization of the orientation and magnitude values of the pixels in an image [3, 7–10]. That is, it defines an image in terms of groups of local histograms that point to local regions of an image. The features of HOG can be seen on a grid of rose plots spaced uniformly. The grid dimensions depend upon the size of the cell and image. Thus, every rose plot depicts the gradient orientations distributed in a HOG cell. In a cell histogram, the length of the A B C D Figure 2. Depiction of rectangle features shown relative to the detection window.
Figure 1 Depiction of rectangle features shown relative to the detection window.
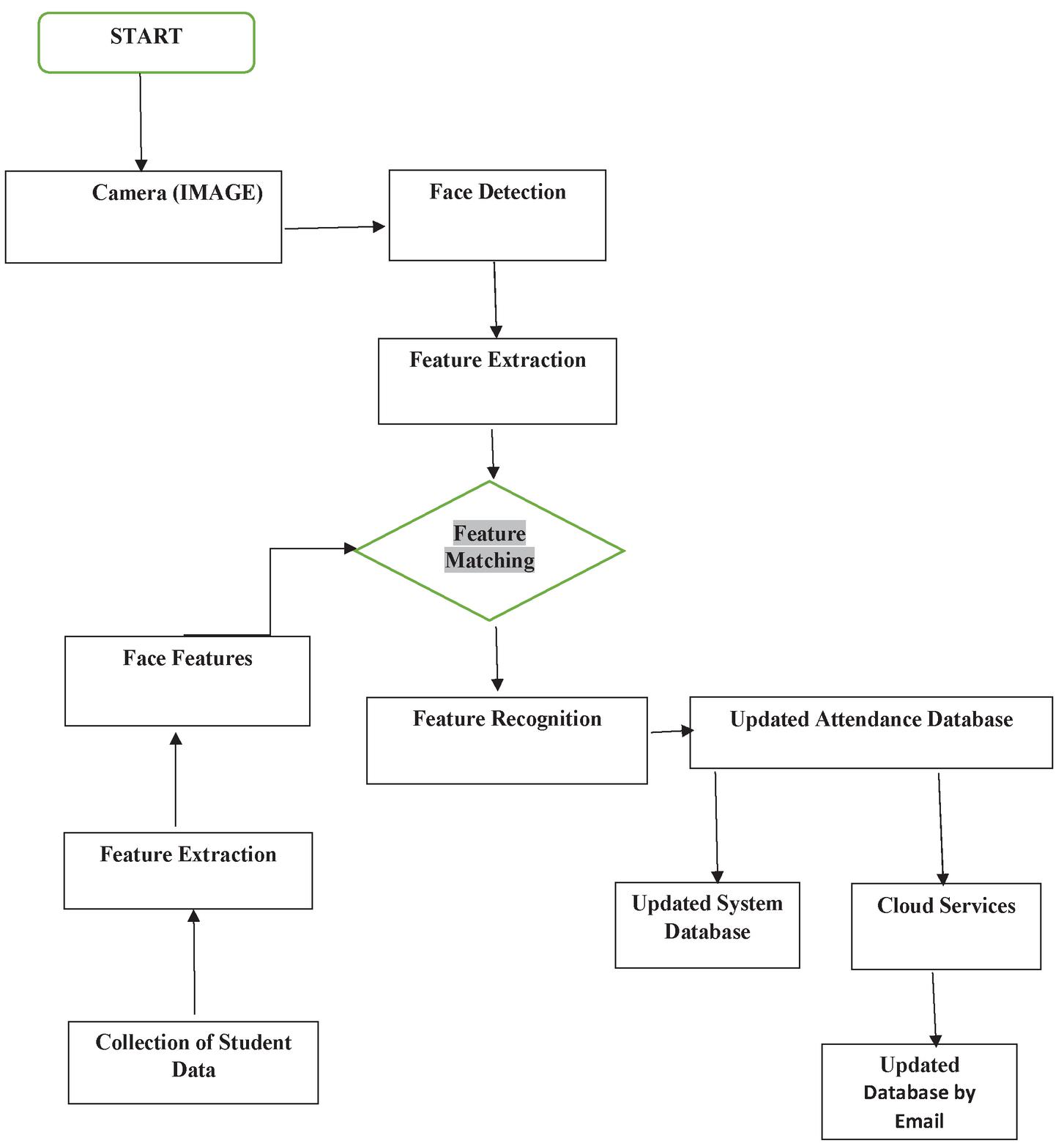
A. Flowchart:
B. Cloud Services (IFTTT):
Figure 2 IFTTT service.
C. Working:
The entire work is divided into two processes.
1. Recognizing the person face.
2. Storing and sending the data records.
D. Recognizing the person face.
Step 1: Finding all the Faces
Encode a picture using the HOG algorithm to create a simplified version of the image. Using this simplified image, find the part of the image that most looks like a generic HOG encoding of a face.
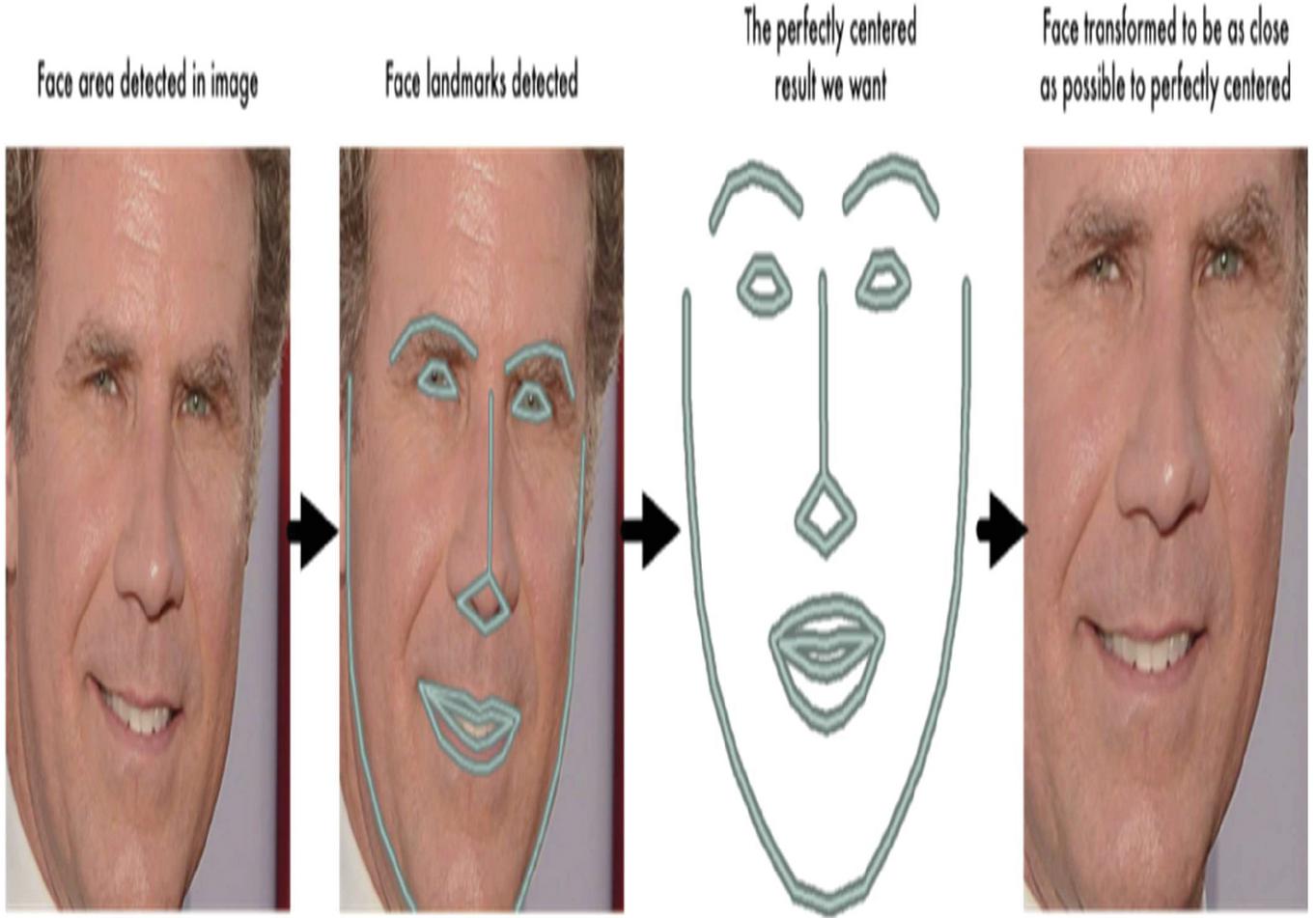
Step 2: Posing and Projecting Faces
Figure out the pose of the face by finding the main landmarks in the face. Once we find those landmarks, use them to warp the image so that the eyes and mouth are centered.
Step 3: Encoding faces
Pass the centered face image through a neural network that knows how to measure features of the face. Save those 128 measurements.
Step 4: Finding the person’s name from the encoding
Looking at all the faces we’ve measured in the past, see which person has the closest measurements to our face’s measurements. That’s our match!
– Storing and sending the data records.
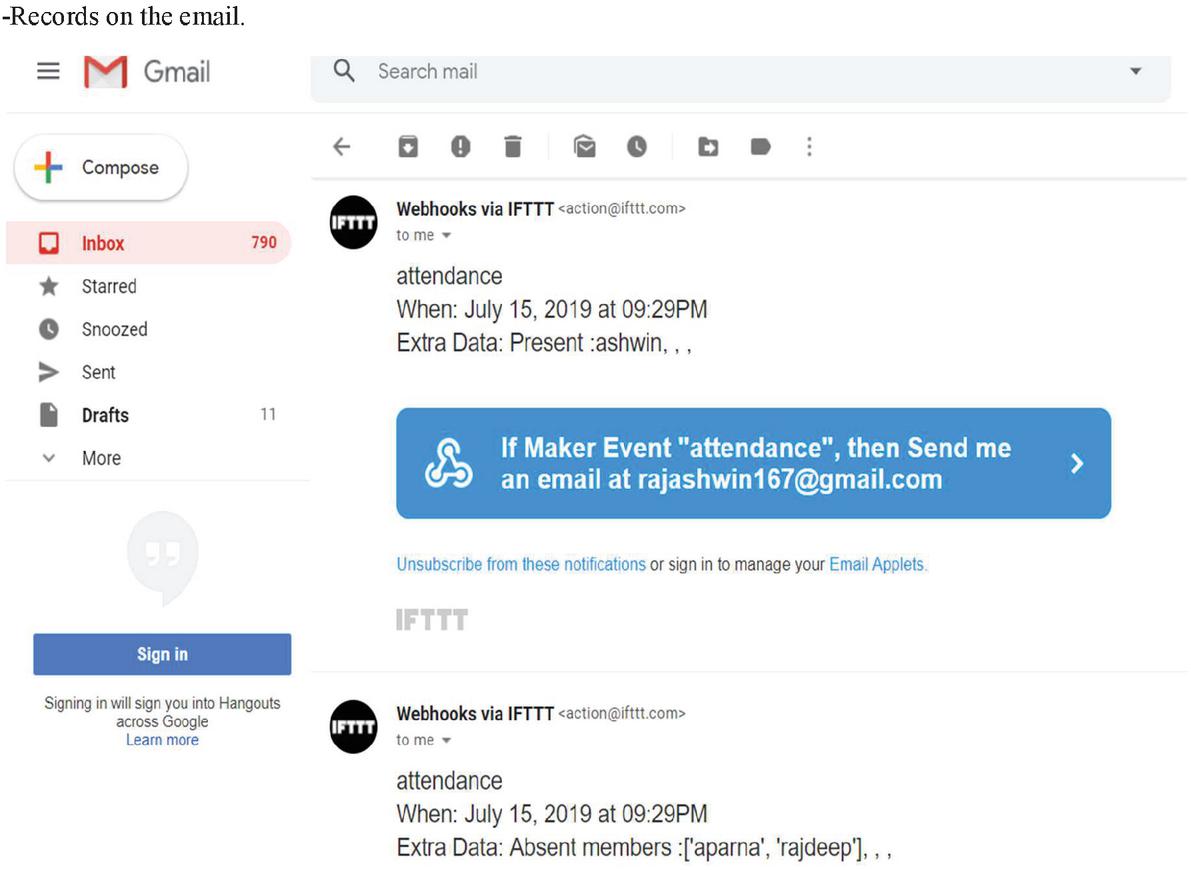
Here we are using ifttt to send a mail to user provided email id. Using the ifttt service. It works on the programing conditional statement If This Then That. The automations are accomplished via applets which are sort of like macros that connect multiple apps to run automated tasks. An applet is created to link a triggering action(face recognition) to onset an event(sending an email).
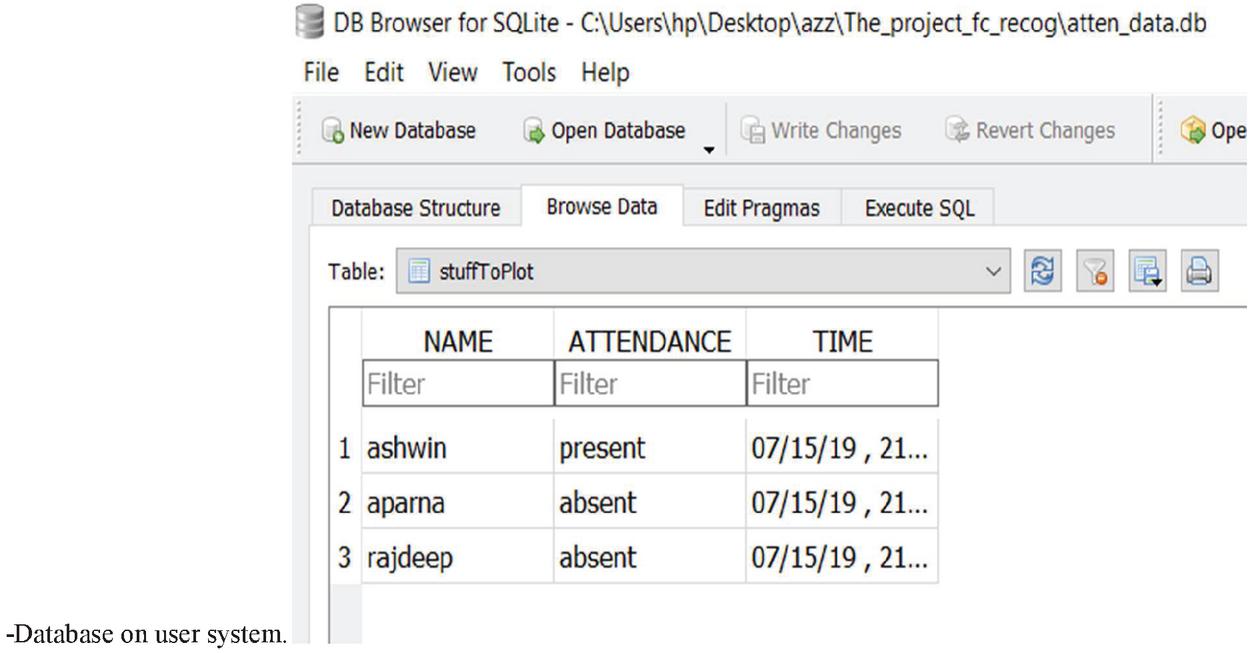
Now for storing database on the system we have SQLite3. We use sql queries to create tables and feed information in it. Each time system runs the data get automatically uploaded in the database.
Figure 3 Shows the use of landmarks and transforming the images to be close as possible for perfect centering.
E. Validation of results:
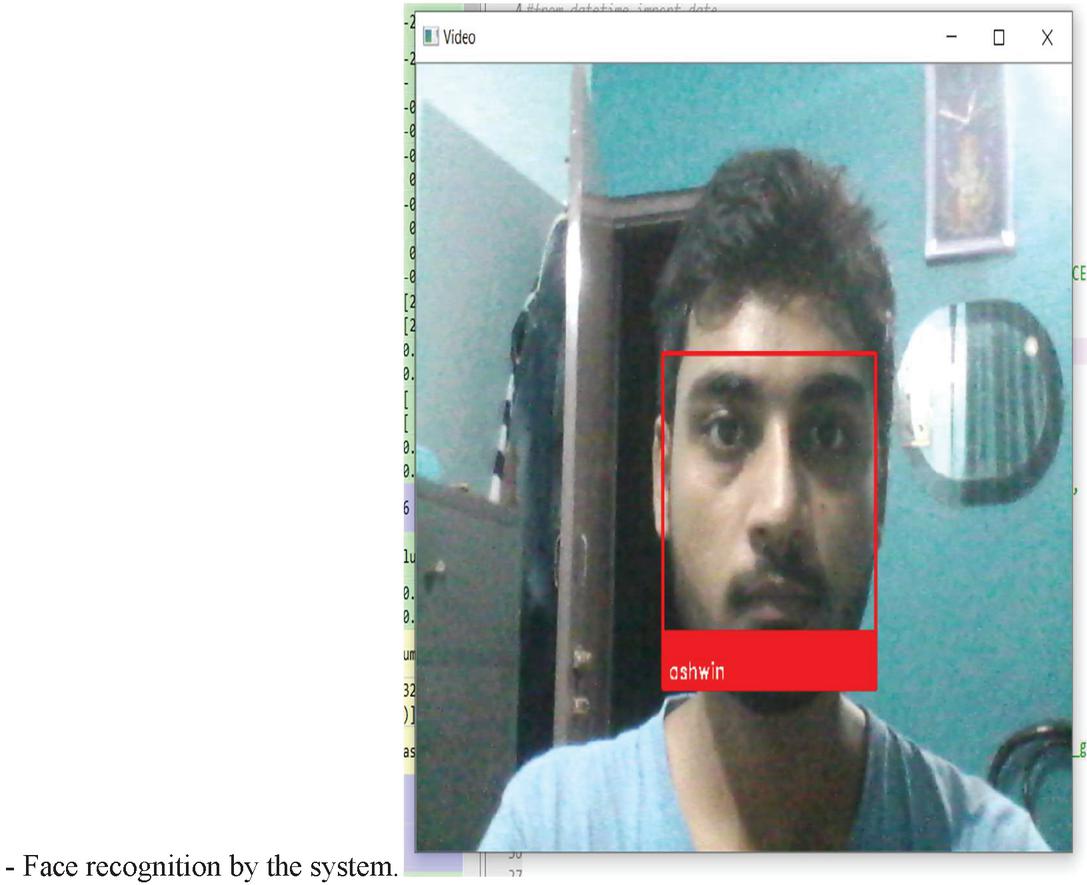
Figure 4 Shows that the camera captures the video on live mode and extracts the face for recognition.
Figure 5 Shows the tabulated record of student’s attendance. Here SQLite is used for database management.
Figure 6 Shows attendance records send to the user email at the real time. Figure also shows the records are sent and updated to same email.
3 Comparative Study
The study of this paper is compared to the research related on this topic. The study related to reference number – [5] uses the concept of taking multiple images of a person and storing it on a separate space. This method uses much space and consumes extra time for creating a training dataset whereas this method uses deep neural network concept which is smart and efficient enough to train itself by providing a single image of a person. So time will be reduced and storage dependency will also be sorted.
The study of reference number – [9] use the technique of storing records on the specific system where our model stores the records on the user system as well as send the real time attendance data to user’s email using cloud system. So the data can be easily accessed from any place.
4 Conclusion
The system uses the camera of the computer to recognize the students by showing their name below their picture. As soon as it identifies the student an email is generated and sent to the address provided by user to notify about its attendance. After the identification of all students, the camera is closed and then name of the absent students are called out with the help of speech synthesizer. Then with the help of the Browser we can see the database which was created having the entry fields of name, attendance, date and time.
Acknowledgement
I am thankful to Dr. Imteyaz Ahmad, HOD,Department of ECE BIT Sindri, I.P Sinha and Saurav kumar of Dthingz lab, Ranchi.
References
[1] Tiwary H “Live Attendance System via Face Recognition” IJRASET, Vol. 6, Issue-4, April 2018, pp. 3891–3897.
[2] Dalal, N., Triggs, B.: Histogram of oriented gradients for human detection. In: IEEE Computer Society Conference on Computer Vision and Pattern Recognition, vol. 1, pp. 886–893 (2005)
[3] Korkmaz, S.A., Akçiçek, A., Bínol H., Korkmaz, M.F.: Recognition of the stomach cancerimages with probabilistic HOG feature vector histograms by using HOG features. In: IEEE International Symposium on Intelligent Systems and Informatics (SISY), pp. 339–342 (2017).
[4] Alina L. Machidon, Octavian M. Machidon, Petre L. Ogrutan, “Face Recognition Using Eigenfaces Geometrical PCA Approximation and Neural Networks”, Telecommunications and Signal Processing (TSP) 2019 42nd International Conference on, pp. 80–83, 2019.
[5] Nuruzzaman Faruqui, Mohammad Abu Yousuf, Md. Fazlul Karim Patwary, “Automatic Examinee Validation System using Eigenfaces”, Advances in Science Engineering and Robotics Technology (ICASERT) 2019 1st International Conference on, pp. 1–7, 2019.
[6] Vegnish Rao Paramesura Rao, Chamode Anjana Hewawasam Puwakpitiyage, Dalia AbdulKareem Shafiq, Farhana Islam, Dini Oktarina Dwi Handayani, Hamwira Yacoob, Teddy Mantoro, “Design and Development of Facial Recognitionbased Library Management System (FRLMS)”, Computing Engineering and Design (ICCED) 2018 International Conference on, pp. 119–124, 2018.
[7] Khem Puthea, Rudy Hartanto, Risanuri Hidayat, “A review paper on attendance marking system based on face recognition”, Information Technology Information Systems and Electrical Engineering (ICITISEE) 2017 2nd International conferences on, pp. 304–309, 2017.
[8] Nabeelanaaz Suri, Maheshwari Marne, Mohini Ghotekar, Utkarsha Pacharaney, “Design of facial features based hospital admission using GSM”, Inventive Computation Technologies (ICICT) International Conference on, vol. 1, pp. 1–6, 2016.
[9] Adam Geitgey, “Modern Face Recognition with deep Learning”, 2016.
[10] Codacus – OpenCV face recognition, Nov 4 2016.
[11] Open cv – “Face detection using haar cascades”.
[12] M. Turk, A. Pentland, Eigenfaces for Recognion, Journal of Cognitive Neurosicence, Vol. 3, No. 1, Win. 1991, pp. 71–86.
Biographies

Imteyaz Ahmad received his master’s degree from VJTI, Matunga. Mumbai-19 under Mumbai University, Mumbai, India and Ph.D. degree from BIT Sindri under Vinoba Bhave University, Hazaribagh, India. He is currently a Associate Professor with the department of Electronics and Communication Engineering, BIT Sindri, Dhanbad, India. His current research interests include Bio-instrumentation and Bio-medical signal processing.

Ashwin Raj is a 3rd year (5th sem) B.Tech Electronics and Communication Engg. student at B.I.T. Sindri from 2017. He is majoring in Electronics and Communication Engg. He is having a 4 months experience as a Role of Backend Development Intern at FitnessBite Gurgaon. Ashwin also get rewarded the First Prize at The Hackathon 2020 Conducted by N.I.T. Rourkela. Ashwin is having a keen interest in technologies Like Web development and Machine learning. He has worked on various projects and Technologies with the Head of Department and his Batchmates.

Aparna Raj is a 3rd year B.Tech, Electronics and Communication Engineering student at B.I.T. Sindri from 2017.She is having a 1 month experience as a Frontend Developer Intern at ProgIST. She has also done vocational training in Machine Learning and IOT at Dthinz Lab,Ranchi. Aparna is having a keen interest in React Js and has deployed a social connect website.
Journal of Mobile Multimedia, Vol. 17_1-3, 115–126.
doi: 10.13052/jmm1550-4646.17135
© 2020 River Publishers