STeSH: Intelligent Speech Technology Enabled Smart Home Automation Using IoT
Santosh Kumar Sahoo1, Sushant Kumar Pattnaik2, Soumya Ranjan Samal3, 4,*, Chinmay Kumar Nayak5, Jitendra Kuma Das2 and Vladimir Poulkov3
1CVR College of Engineering, Hyderabad, Telangana, India
2School of Electronics Engineering, KIIT University, Bhubaneswar, India
3Faculty of Telecommunications, Technical University of Sofia, Bulgaria
4Silicon Institute of Technology, Bhubaneswar, India
5Faculty of Emerging Technologies, Sri Sri University, Cuttack, India
E-mail: santosh.kr.sahoo162@gmail.com; sushanta.pattnaik@silicon.ac.in; sranjansamal@tu-sofia.bg; cknayak85@gmail.com; jkdasfet@kiit.ac.in; vkp@tu-sofia.bg
*Corresponding Author
Received 12 August 2021; Accepted 20 February 2022; Publication 30 June 2022
Abstract
Due to the advancement in recent technologies and emergence of Internet of Things (IoT), Smart Home Automation (SHA) plays a vital role in today’s lifestyle. Many users are showing their keen interest to move towards this era of digital transformation in order to take the potential benefits of such intelligent and smart application. Traditional smart home systems have several limitations e.g. connectivity, coverage area, device dependability, platform supportability etc. which makes the system less sustainable. In this paper, the proposed technique introduces a novel scheme to operate the devices in an intelligent manner. The scheme implements a system named as “Speech Technology enabled Smart Home (STeSH)”, which supports voice assisted home automation with extreme security and range-free localization. The idea of the proposed technique is to integrate the power of IoT with classical home automation by using an advanced speech technology service. The entire processing of Speech Enabled Services (SES) is applied with this proposed technique and the detailed analysis is presented with proper experimental proof.
Keywords: Speech technology, IoT, smart home automation (SHA), internet enabled services (IES), STeSH, speech recognition.
1 Introduction
This section presents motivation and background studies with a brief introduction followed by a comprehensive state of art of current research. In the end of this section the structure of the paper is also presented.
1.1 Motivation and Background
Now-a-days, smart things and modern technologies are leading over the world with their powerful approaches and provide many intelligent services to mankind to fulfil their needs in many aspects of leisure & commercial domains [1]. In parallel, the communication medium is another growing entity, which supports this gadget to work in intelligent manner to provide ultimate support to people to meet their global communication needs. Specialists do connect computerized gadgets with scientific and authoritative devices to make complex frameworks for quickly extending attributes of uses and physical pursuit. In this context, Internet of Things (IoT) is one of the most emerging technology helps to connect things/devices with each other and can be controlled or monitored remotely through the internet.
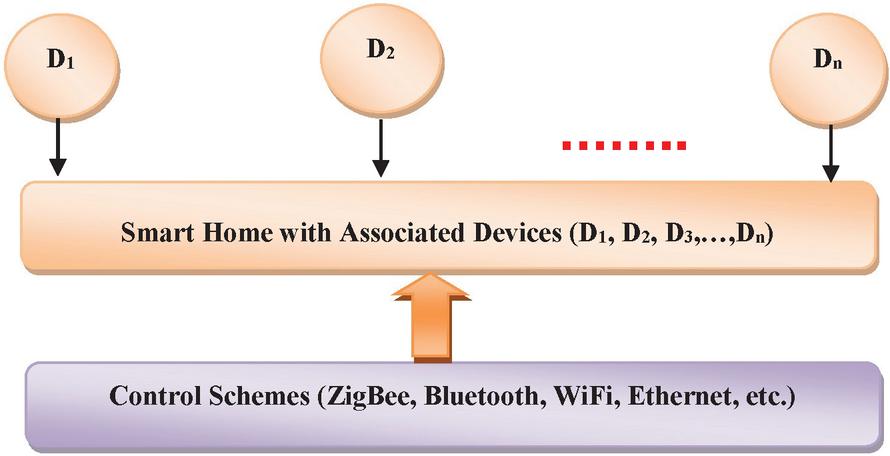
Figure 1 Classical smart home automation system working model.
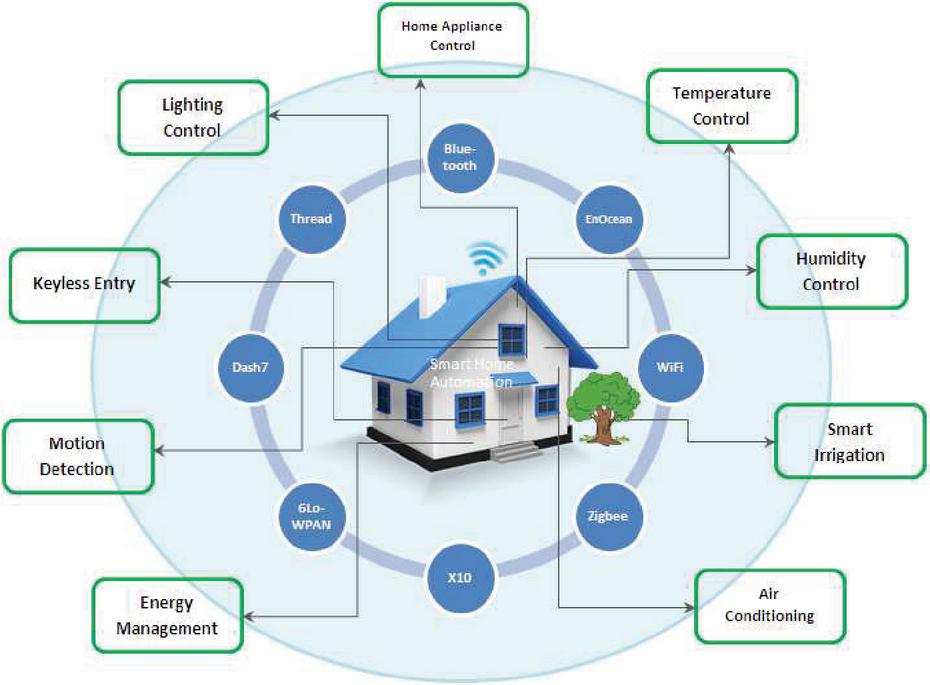
Furthermore, there is a need for switch to systematic mode of everything due to the growth of smart urban areas. So the idea of Smart Home Automation (SHA) system is a thought, which is utilized to make the city shrewd. Since the year of 1990, the concept of smart home has been brought into limelight. SHA is a framework, where individual electronic gadgets/appliances are interconnected with each other to develop an interactive space with the user by exploiting the use of internet enabled services (IES) [2]. A smart home gives solace, security and gives the comfort feel to individuals, but with some additional features like energy efficiency (EE), autonomous functionalities makes it more intelligent [3]. SHA implies the observing and control of white goods wisely for viable utilization. These household appliances ought to be shrewdly interconnected just as to give data for better activities. SHA expanded with IoT gives better adaptability in overseeing and controlling aspects in a more extensive angle. This will bolster the interconnectivity of countless smart homes for better asset use in more extensive territory. Again, with the advent of different speech recognition software like; Alexa-Amazon Echo, Google Assistant, Microsoft Cortana, SILVIA, the demand for SHA is tremendously increasing [4]. As IoT plays an essential role in developing SHA framework, integration of voice recognition techniques/Speech Enabled Services (SES) with IoT brings a new revolution in building intelligent smart home paradigm.
The traditional model of home automation systems as shown in Figure 1, are incorporated with many technologies in both operation and communication wise, but still those models are locked in certain issues and failures [5–7]. Generally, the electrical devices consume power in certain ranges, if you assist the traditional devices along with household device, then the power consumption of the assisting device is more due to its continual operation and uninterrupted power supply (because the system is always in ON state and monitoring the user trigger continuously even if the user don’t want to trigger ON/OFF the device for next few days) e.g. refrigerator/washing machine etc.. The capital expenditure (CapEx) and operation expenditure (OpEx) are very high due to the single board operation as well as low-range of communication, energy efficiency and some other issues are also associated with traditional home automation model [8]. Furthermore, the operation methodology of such classical device is either by means of sending short text message or e-mail to operate the end device which increases the complexity and time consumption. Moreover, the factor of lacking in the classical approach is the range restriction, in which those devices are operated only within 10–15 feet coverage area. So the range restriction is also a crucial issue which needs to resolve over the traditional approach. To avail the fringe benefits, many researchers have been proposed several methodologies for SHA by embedding with various wireless communication technologies. Each proposed methodology leads with respective pros and cons. A comparative analysis of different proposed techniques with their limitations is briefly presented in Table 1.
Table 1 Limitations of different proposed techniques
| Technology | Cost | Data Rate | Communication Range | Speed | Latency Time | EE | Security |
| GSM [9–15] | Expensive | Low | Long range | Fast | Low | Low | Less secure |
| Bluetooth [14–19, 46] | Cheap | Low | Short range | Fast | High | High | Less secure |
| Zigbee [14, 15, 19–25] | Cheap | Low | Mid-range | Low | High | Moderate | Less secure |
| Z-wave [14, 15, 26, 27] | Expensive | Low | Mid-range | Low | High | High | Less secure |
| WiFi [14, 15, 23, 24, 28–34] | Moderate | High | Mid-range | Fast | High | Very Poor | Less secure |
| IoT [34–38, 51–54] | Cheap | High | Wide range | Fast | Low | High | Highly secure |
| Voice Recognition [39–44, 47, 48] | Cheap | High | Wide range | Fast | Low | High | Highly secure |
In this paper, we have proposed a novel methodology which integrates the speech technology along with intelligent communication methods to automate the regular usable devices such as electronic gadgets, charging devices, A.C., Television and other household devices. This work mainly focuses on the application of SES to the SHA services for triggering the electronic devices/things by the mean of customer/user voice. In this context, if any other person or intruders tries to operate the device by using their voice, so there is an operating limitation for the device to manage this situation. Secondly, if a low-range communication scheme such as WiFi, Ethernet, Bluetooth ZigBee, etc. is used, then managing the communication limits properly is also another task. So, these problem statements are the major concern to deal with every SHA services. These constraints are rectified by using our proposed approach called Speech technology enabled Smart Home (STeSH), which collects the user voice and register it for their own home usages at one time and provide the separate authorization and authentication norms for further operations or controlling of devices. In contrast to the authorization and authentication, the STeSH gathers the voice from respective user and verifies its authenticity. If the user is an authorized person, then the device will operate accordingly based on the voice commands raised by the user. And the second concern called communication range limitation is figure-out with IoT enabled services. The following sections clearly illustrate a comparison between existing and proposed system, as well as the result and discussion are clearly presented with the outcome proof and proper prototypical model.
1.2 State of Art
Combining different technologies to facilitate best Quality-of-Service (QoS) and user satisfaction in SHA system, many researches have under gone in various ways. Marie et al. [45] have proposed a SHA framework, which is based on Siri enabled application having the major limitation of device compatibility (supports only in iOS Apple devices). This proposed solution focused on implementation of home automation by speech recognition through Siri application and Raspberry Pi. It has been observed from different tests that, the accuracy and the average latency are 93.33% and 2.12 seconds respectively. The implemented Siri enabled Apple mobile application supports voice translation facility, where the users feel free regarding languages and operate the application in fault free manner. In this proposed technique, only the apple-mobile users are able to use this application and can control the household devices by using this system. In contrast to this, the proposed technique has several shortcomings such as: highly expensive, poor connectivity and platform dependability. A home automation system based on Bluetooth communication technology is presented in [46]. The proposed method uses Bluetooth services with arduino board base. A cell phone is used to send the commands to the Bluetooth and python script programme is for controlling of household devices. The major drawback of the implemented application is low coverage area and incapable for real-time applications. A new approach in SHA is introduced in [47], where human voice is utilized to enable the household devices. In this proposed technique, the system collects the human voice and passes that signal as trigger to respective household device via ZigBee and operates the device according to the respective voice trigger. Certain limitations have been identified in this proposed technique like; programme dependability, pulse based signalling and short-range communication.
The authors of [48] have proposed an approach which integrates Raspberry PI (RPi) as a main controller/CPU to the automation system. The RPi unit collects the voice command from the users and converts the collected commands as a digital signal. Then the converted signals passed as a command to the household devices and allow the device to operate accordingly based on the given trigger from the controller. The proposed solution has several advantages such as; scheduling functions are used to control (turn-on/turn-off) the electrical device, remote web based controlling application can be used to control the electrical equipment’s, but followed with some weaknesses e.g. unable to manage ambient devices, requires strong internet connectivity and processing delay. Jain et al. have proposed and web server based home automation system by using RPi in [49, 50]. Based on the command received through e-mail the home device can be controlled by RPi. A special developed algorithm is used to read the command received from mail and fed to the RPi.
A home automation system with improved security by using IoT technology is introduced in [51, 52]. Here, the authors of [51] tries control the home appliances with the help of smartphone and low-range communication protocol like WiFi. The proposed system is also capable of detecting fire accidents. Where in [52], the authors have used Thing Speak with Blynk application to control and monitor the home appliances with the help of smart mobile. This proposed solution also facilitates safety protection for fire and other security issues. An interactive IoT based home automation system is proposed in [53]. This proposed system includes Google assistant to control the household devices based on voice based speech recognition technique. Based on the results and experimental studies in various scenarios, the system performance is observed to be 100% accurate. A SHA with customizable Graphical User Interface (GUI) and low-cost embedded system with internet connectivity is proposed in [54]. In this work, the home appliances can be controlled through a smart phone or any computer based application. The inclusion of GUI facilitates the user demands which are further communicated to control system via wireless technology. The control system incorporates a client-server based model for remote accessing purpose.
A hybrid-based intrusion detection system model for intruder detection is proposed in [55]. The proposed logic uses genetic algorithm (GA) with fuzzy to handle large data volume NSL-KDD dataset to improve effectiveness of detection and to reduce misclassification alarm rate. In addition, component analysis (CA) principle is used to improve the efficiency and accuracy by eliminating the irrelevant/redundant data from large volume of data set. A non-intrusive approach by using machine learning (ML) for personalized aid living is proposed in [56]. This proposed solution presents a novel modelling scheme for technology instantiation of big data, IoT and non-invasive personalization collecting data from open standard IoT devices. Anathi et al. have proposed an artificial intelligence (AI) based dynamic network traffic restriction methodology by using MAC address verification strategy in [57].
Nevertheless, the entire above quote clearly describes the existing mechanism of SHA is failed to satisfy the user needs based on four different factors such as: time consumption, processing delay, cost, complexity and security. So, that a new approach is required to resolve all such issues and provide an efficient mechanism of operating household devices over home in intelligent and secured manner as well as consider regarding the range issues over existing approach and provide solution for that too. In this work, the proposed logic of STeSh uses the dataset nature to identify the face of the user. The robustness of the proposed system is verified in dual level authentication process i.e. face recognition and speech verification. We have also included the nature of MAC address verification process to eliminate the time consumption over triggering of loads which leads the system to perform faster compare to all other existing schemes.
1.3 Structure of the Paper
The rest part of the current paper is organized as follows,
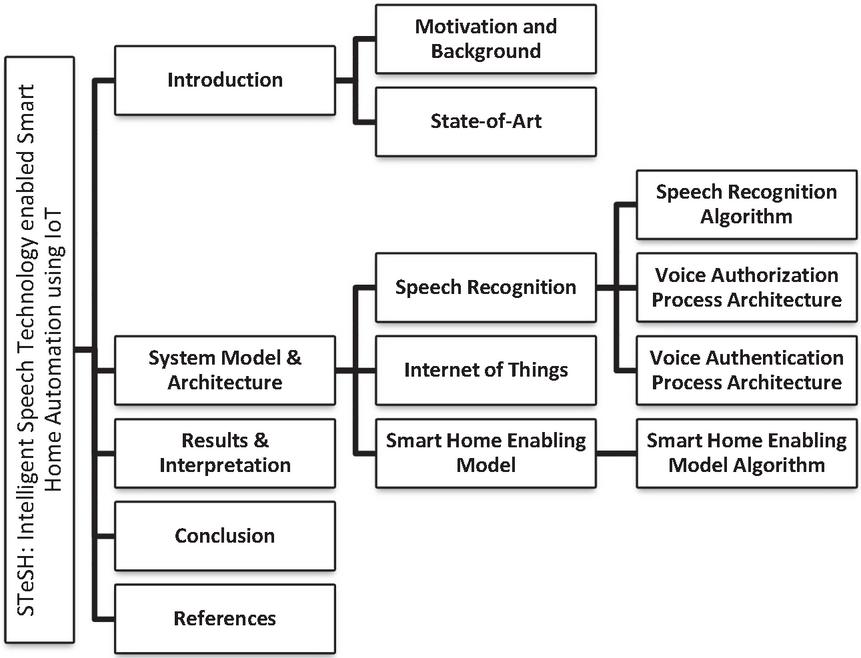
Figure 2, illustrates the outline of the paper. The proposed system model and the process architecture are described in Section 2 whereas in Section 3, result and interpretation is realized. To end, the conclusion and future work is discoursed in Section 4.
Figure 2 Schematic representation of the structure of this paper.
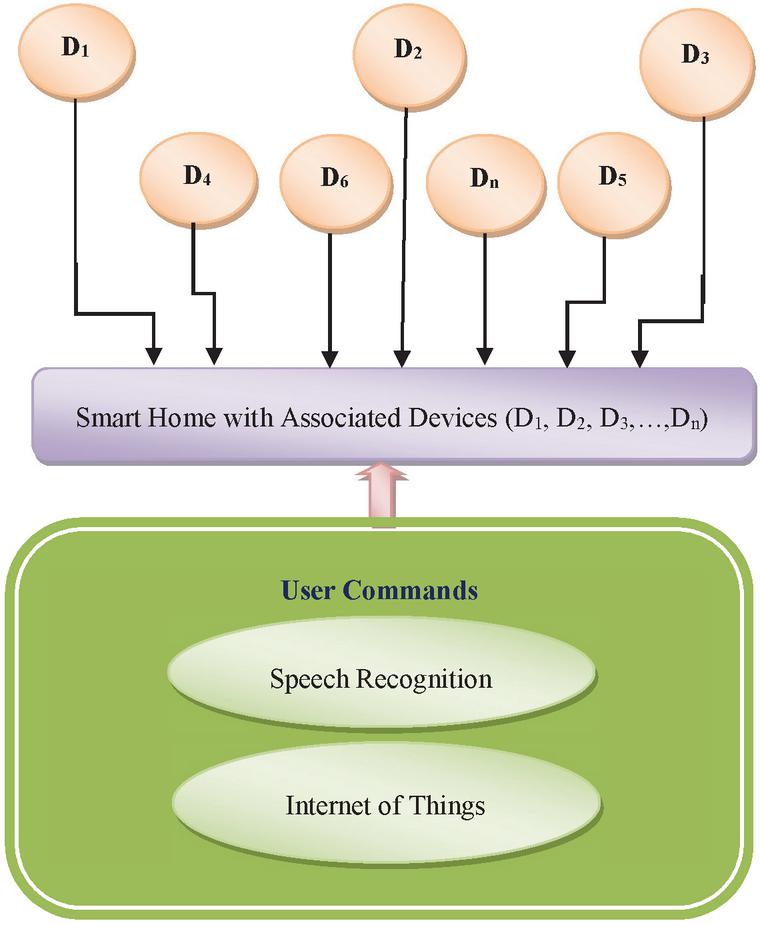
Figure 3 Proposed system flow diagram.
2 System Model & Architecture
This proposed STeSH technique integrates different emerging technologies together, promising it as a more robust and secured mechanism over the operation of voice enabled smart home controlling. The integrated intelligent features are as follows: (A) Speech Recognition, (B) IoT and (C) SHA. All these will be described in details further. The proposed system model is Figure 3.
2.1 Speech Recognition
The Speech Recognition methodology collects the user speech and process the speech into many norms with voice-based feature extraction strategy. In this method each and every voice pulses are segregated and compare those pulses with the authorized user voice. If the user input voice signal is matched with the registered/authorized user voice, then the voice recognition mechanism recognize the voice and gives the positive trigger to the controller to operate the respective household device. The algorithm in Table 2, illustrates the logic of speech recognition algorithm step by step in detail.
Table 2 Algorithm: Speech Recognition
| ALGORITHM: SPEECH RECOGNITION |
| Input: Analog Human Voice |
| Output: Digital Conversion and Recognized Boolean Result |
| Step-1: Importing the respective Speech Recognition library. |
| Step-2: Create an object to assign the imported speech variables from library. |
| Step-3: Creating a class and object for audio recognition and it will recognize the audio is extracted from human voice or else any recorded medium (Ex. Class Audio Recognizer (Audio Source)). |
| Step-4: Assign the recognized voice into a variable (Ex. Aud Audio_Recognizer [input]). |
| Step-5: Creating a loop for reading a voice from first to last. |
| Step-6: With Aud.Read() as Input, this statement will start the loop. |
| Step-7: Raise the printing statement to intimate to the user to give respective input voice to the system. |
| Step-8: System automatically changes the mode from query the user to listen the voice as; |
| Aud Audio_Source.Listen (Input). |
| Step-9: Add the exception statements to monitor the steps from 1 to 9 for managing the system robustness and fault tolerance from unpredictable exceptions. |
| Step-10: Extracting Proper Audio from input and change the modulation from input audio collected from user. |
| Step-11: Analyze the audio input and store the result into defined Boolean variable (Ex. Boolean R). |
| Step-12: R = Resultant_Voice (Input). |
| Step-13: Return R. |
The following pseudo-code illustrates the algorithm logic of speech recognition and describes the flow implementation.
| PSEUDOCODE: SPEECH RECOGNITION |
| Import Speech-Recognition |
| define Speech-Recognition as SR_1; |
| define Audio-Identifier as Aud; |
| SR_1 = Audio_Recognizer (Audio_Source); |
| With SR_1.MicrophoneObject() as Input: |
| PrintStmt(“Input Voice Fully from start to End”); |
| Aud = Audio_Source.Listen(Input); |
| Try |
| PrintStmt(“System think you said improper word:” + |
| Audio_Source.Listen(Input)); |
| Exception SR_1.UnknownValueError |
| PrintStmt(“Could not understanding the audio input:” + |
| Audio_Source.Listen(Input)); |
| Exception SR_1.RequestSystemError as expc: |
| PrintStmt(“System Error{0}:” + expc); |
| End Try |
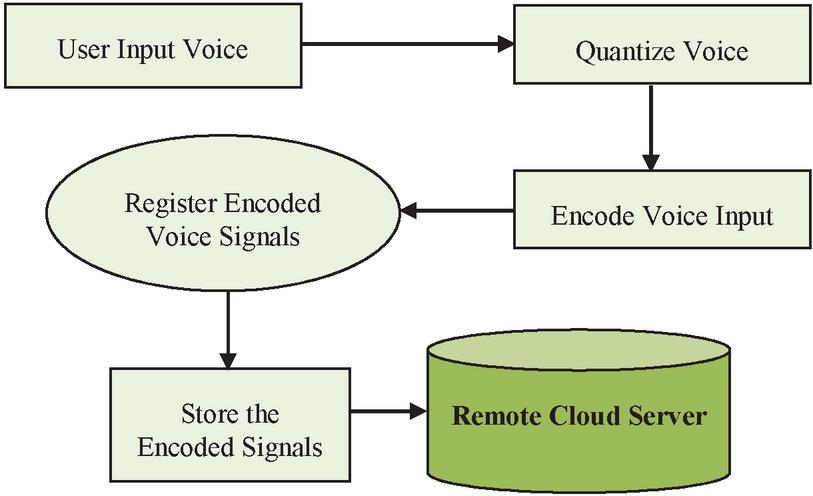
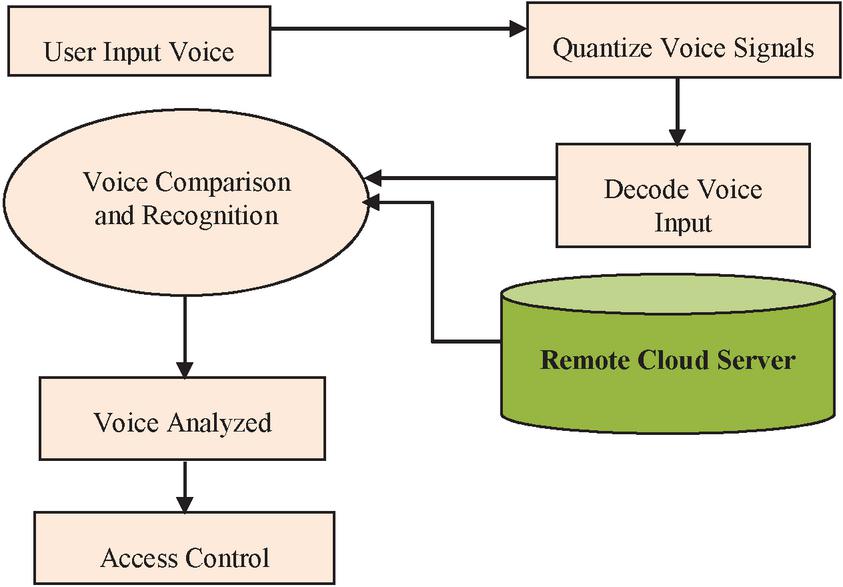
Figure 4 Voice authorization process architecture.
A schematic representation of voice authorization process is shown in Figure 4. This methodology uses Google based voice assistance, which collects the user voice. The input user voice then processed (quantized and encoded) and the encoded user voice signal is stored in a remote cloud server. Then the registered voice signal is compared with the input voice signal for authentication purposes. If the registered/authorized voice signal satisfies the authentication process, provides the access permission to operate the corresponding devices. If the input/collected voice signal doesn’t match with the authorized voice signals, then the system informs regarding the authentication error. The Figure 5 illustrates the overall work flow model architecture of voice authentication process.
Figure 5 Voice authentication process architecture.
2.2 Internet of Things (IoT)
IoT technology is ruling over the world with its power and connectivity, which is nothing but a refined form of network. IoT interconnect the remote cloud server with local devices, so that the user can communicate from anywhere at any time without any restrictions. By using IES user can speak and operate the device from anywhere in the globe without any range restrictions. The application of IoT technology is illustrated in the proposed approach with the help of Equations (1) and (2) [58];
| (1) | |
| (2) |
Where, is physical objects/things, refers to controller, sensors and actuators, indicates IES, indicates the base station (BS) signal strength during connection establishment, indicates the total signal strength for the respective coverage range w.r.t. and surroundings, indicates the associated port number with the established connection and indicates the total traffic ratio over establishing the internet connection.
Figure 6 Internet of things service model.
2.3 Smart Home Enabling Model
As smart home services allows user to operate the household devices from anywhere and at any time around the globe without any range restrictions. This process happens only if the devices are properly bound over communication medium. This support is assisted by means of IES over the proposed work model along with speech recognition technique. The speech recognition system receives voice from the user and process the input voice signal according to authentication norms. If the authenticated user is trying to access the device means it permits the flow. But if an intruder is trying to login into the system, the access permission is denied. The proposed framework is more secured and robust compared to the classical working model and it is more convenient to work with the proposed model because of its unlimited range support and easy operation. The proposed system provides efficient and intelligent working model in results, which will be illustrated clearly in results further.
The Equations (3) and (4) illustrate the nature of collecting human voice and maintain it into the repository.
| (3) |
Here, represents the storage of user voice input and indicate the upper limit variations, is the collected input voice range signals which is starting from 1 and ending in .
| (4) |
Table 3 Algorithm: Speech Recognition
| ALGORITHM: SMARTHOME ENABLING MODEL |
| Input: Human Voice or Recorded Speech input |
| Output: Convert Audio Transcriptions to Text and Triggered the Respective Load |
| Step-1: Importing the respective Speech Recognition library. |
| Step-2: Create an object to assign the imported speech variables from library. |
| Step-3: Declare a Voice_Recognizing class to clearly recognize the speech from user side. We are using Google_Speech recognition library over here. |
| Step-4: Speech file supported by Speech_Recognition in the format of “WAV/MP4”. |
| Step-5: Google recognizer reads English usually but need to add some language libraries for multi-language supportivity. |
| Step-6: Match the input voice from the user voice repository. |
| Step-7: Identify the voice robustness and authenticity. |
| Step-8: Trigger the Respective Load according to the corresponding input. |
| Step-9: Return triggered load details to user reflection area. |
| Step-10: Stop gathering Voice and go to Step-3. |
Where, illustrates the storage of user voice storage repository and ‘’ indicates the upper range of the repository, is the collected input voice range signals which is starting from 1 and ending in . All these voices are stored in order to the repository for managing the secured voice-based recognition to operate the smart home without any security issues. Following the Equations (2) and (3), Table 3 illustrates STeSH algorithm implemented smart home enabling model in detail.
3 Results and Interpretation
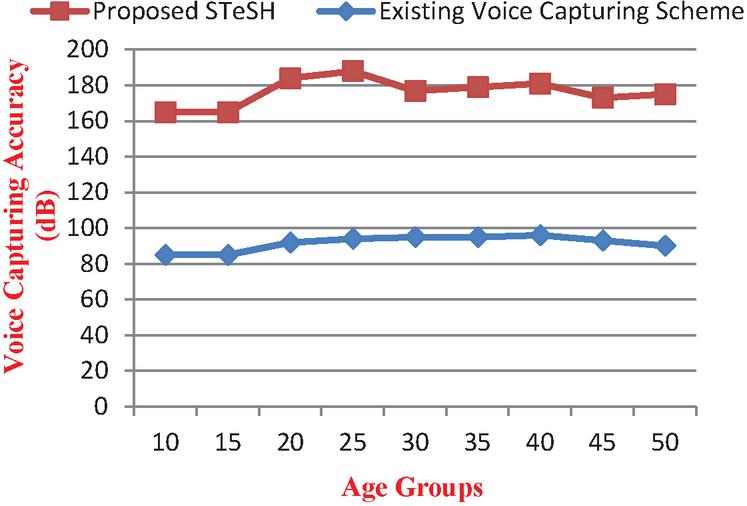
In this section, the results of proposed solution are explained in detail. Based on the algorithms presented in Section 2 and evaluating the outputs with the traditional model it assures that; the proposed system is more robust and EE. A comparative analysis between the existing and proposed system in terms of voice capturing accuracy and performance ratio is presented in Table 4. This comparison is analysed by taking 50 different samples from persons of dissimilar age groups between 10 to 60.
Table 4 Voice capturing accuracy levels
| Age Group | Existing Voice Capturing Accuracy | STeSH Voice Capturing Accuracy |
| 10 to 15 | 80% | 85% |
| 16 to 20 | 79% | 92% |
| 21 to 25 | 78% | 94% |
| 26 to 30 | 82% | 95% |
| 31 to 35 | 84% | 95% |
| 36 to 40 | 85% | 96% |
| 41 to 45 | 80% | 93% |
| 46 to 50 | 85% | 90% |
Figure 7 Existing model vS STeSH voice capturing accuracy levels.
The Figure 7 illustrates the graphical comparison view of the existing and proposed system voice capturing accuracy and performance ratio. From this graph it is clearly visible that the STeSH voice capturing accuracy level is better than the existing model.
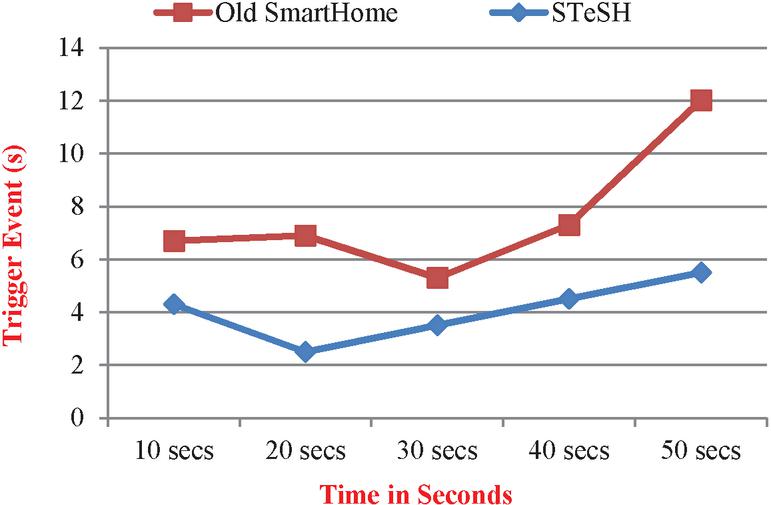
Figure 8 Time delay between existing model vs STeSH.
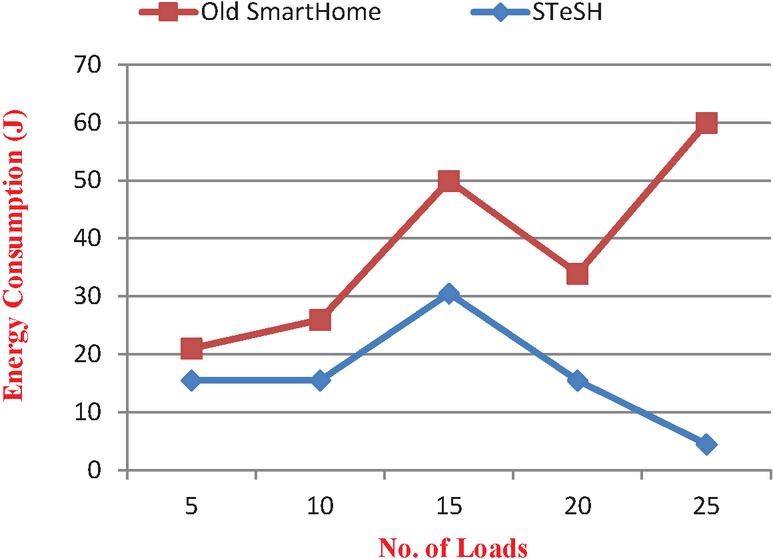
Figure 9 Energy consumption between existing model vs STeSH.
The Figure 8 represents a comparison between the existing home automation technique and STeSH home automation technique in terms of time delay to trigger the loads according to user control. It can be observed from the analysis that the processing delay of STeSH is quite small as compared to the existing model. The Figure 9 illustrates a comparison between the existing home automation technique and the STeSH based home automation technique energy consumption ratio. The graph clearly shows that the proposed model consumes less power as compared to the existing traditional model. This reduction in energy consumption facilitates green communication by minimizing emission.
4 Conclusion
The proposed STeSH based SHA system is implemented satisfactorily with advanced speech technology-oriented processing and intelligent operational features such as Voice/Speech Recognition strategy and IoT. The Google Assistant is used to collect the user voice and send it to the remote server for processing and storing. The server-side system converts the entire speech signals into encoded raw commands and stored it into the remote cloud server with proper access right specifications. Once the user authenticates into the system, automatically it crosschecks the voice input with the processed voice input over the server. If the authentication is successful, then the respective user is allowed to operate the home devices without any interruptions otherwise the system blocks the user to proceed further. From the result analysis it confirms that, the proposed SHA system ensures secured and robust way to automate the home with easy and scalable way. This proposed methodology also improves the EE of the SHA system.
References
[1] David J. et al. (2021). The Internet of Everything: Smart things and their impact on business models, Journal of Business Research, Volume 122, 2021, pp. 853–863, ISSN 0148-2963, https://doi.org/10.1016/j.jbusres.2019.12.035.
[2] Kumar, S., Tiwari, P. and Zymbler, M., (2019). Internet of Things is a revolutionary approach for future technology enhancement: a review. Journal of Big Data 6, 111, Springer. https://doi.org/10.1186/s40537-019-0268-2.
[3] Stolojescu-Crisan, C., Crisan, C., and Butunoi B-P., (2021). An IoT-Based Smart Home Automation System, Sensors, 21(11):3784, https://doi.org/10.3390/s21113784.
[4] Swain, K.P., et al., (2021). Academic Students Attendance System: A Case Study of Alexa Skill Development, In: Sabut S.K., Ray A.K., Pati B., Acharya U.R. (eds) Proceedings of International Conference on Communication, Circuits, and Systems, Lecture Notes in Electrical Engineering, vol. 728. Springer, Singapore, https://doi.org/10.1007/978-981-33-4866-0\_1.
[5] Rasha El-Azab, (2021). Smart homes: potentials and challenges, Clean Energy, Volume 5, Issue 2, Pages 302–315, https://doi.org/10.1093/ce/zkab010.
[6] Sathesh and Hamdan, Y. B., (2021). Smart Home Environment Future Challenges and Issues - A Survey, Journal of Electronics and Informatics, 3(1), 1–14, doi:10.36548/jei.2021.1.001.
[7] Lobaccaro, G., Carlucci, S., and Löfström, E., (2016). A Review of Systems and Technologies for Smart Homes and Smart Grids, Energies, 9(5):348, https://doi.org/10.3390/en9050348.
[8] Kehinde, L., and Rafsanjani, H. N., (2021). Trends, benefits, risks, and challenges of IoT implementation in residential and commercial buildings, Energy and Built Environment, ISSN 2666-1233, https://doi.org/10.1016/j.enbenv.2021.01.009.
[9] Hussain A. F., et al., (2021). Zigbee and GSM Based Security System for Business Places, International Conference on Advance Computing and Innovative Technologies in Engineering (ICACITE), pp. 264–267, doi: 10.1109/ICACITE51222.2021.9404577.
[10] Jothi, T. M., et al., (2018). GSM Based Home Environment Monitoring System, 2nd International Conference on Trends in Electronics and Informatics (ICOEI), pp. 1263–1268, doi: 10.1109/ICOEI.2018.8553839.
[11] Choudhury, B., et al., (2015). Design and implementation of an SMS based home security system, IEEE International Conference on Electrical, Computer and Communication Technologies (ICECCT), pp. 1–7, doi: 10.1109/ICECCT.2015.7226115.
[12] Sharma, R. K. et al., (2014). Android interface based GSM home security system, International Conference on Issues and Challenges in Intelligent Computing Techniques (ICICT), pp. 196–201, doi: 10.1109/ICICICT.2014.6781278.
[13] Teymourzadeh, R., et al., (2013). Smart GSM based Home Automation System, IEEE Conference on Systems, Process & Control (ICSPC), pp. 306–309, doi: 10.1109/SPC.2013.6735152.
[14] Danbatta, S. J. and Varol, A., et al., (2019). Comparison of Zigbee, Z-Wave, Wi-Fi, and Bluetooth Wireless Technologies Used in Home Automation, 7th International Symposium on Digital Forensics and Security (ISDFS), pp. 1–5, doi: 10.1109/ISDFS.2019.8757472.
[15] Withanage, C., et al., (2014). A comparison of the popular home automation technologies, IEEE Innovative Smart Grid Technologies – Asia (ISGT ASIA), pp. 600–605, doi: 10.1109/ISGT-Asia.2014.6873860.
[16] Asadullah, M. and Ullah, K., (2017). Smart home automation system using Bluetooth technology, International Conference on Innovations in Electrical Engineering and Computational Technologies (ICIEECT), pp. 1–6, Karachi, Pakistan.
[17] Anandhavalli, D.; Mubina, N.S. and Bharath, P., (2015). Smart Home Automation Control Using Bluetooth and GSM, Int. J. Inf. Futur. Res., 2, 2547–2552.
[18] Anitha, G., et al., (2021). Bluetooth Based Home Automation and Security System, Journal of Physics: Conference Series, Bristol Vol. 1916, Iss. 1, DOI: 10.1088/1742-6596/1916/1/012106.
[19] Baraka, K., et al., (2013). Low Cost Arduino/Android-Based Energy-Efficient Home Automation System with Smart Task Scheduling, 5th International Conference on Computational Intelligence, Communication Systems and Networks, pp. 296–301, Madrid, Spain.
[20] Zamora-Izquierdo, M.A., Santa, J. and Gomez-Skarmeta, A.F., (2010). An Integral and Networked Home Automation Solution for Indoor Ambient Intelligence. IEEE Pervasive Comput. 2010, 9, 66–77.
[21] Froiz-Míguez, I., et al., (2018). Design, Implementation and Practical Evaluation of an IoT Home Automation System for Fog Computing Applications Based on MQTT and ZigBee-WiFi Sensor Nodes. Sensors, 18, 2660.
[22] Li, Z.M., Song, M., and Gao, L., (2014). Design of Smart Home System Based on Zigbee. Appl. Mech. Mater., 635–637, 1086–1089.
[23] Vivek, G. and Sunil, M., (2015). Enabling IOT services using WIFI-ZigBee gateway for a home automation system, IEEE International Conference on Research in Computational Intelligence and Communication Networks (ICRCICN), pp. 77–80, Kolkata, India.
[24] Huang, F.-L., and Tseng, S.-Y., (2016). Predictable smart home system integrated with heterogeneous network and cloud computing, International Conference on Machine Learning and Cybernetics (ICMLC), Volume 2, pp. 649–653, Jeju, Korea,
[25] Jadhav, P., Chaudhari, A.and Vavale, S. (2014). Home Automation using Zigbee Protocol, International Journal of Computer Science and Information Technologies, Vol. 5(2), 2014, 1778–1780.
[26] Ozeer, U., et al., (2019). Designing and Implementing Resilient IoT Applications in the Fog: A Smart Home Use Case. In Proceedings of the 2019 22nd Conference on Innovation in Clouds, Internet and Networks and Workshops (ICIN), pp. 230–232, Paris, France,
[27] Yassein, M. B., Mardini, W., and Khalil, A., (2016). Smart homes automation using Z-wave protocol, International Conference on Engineering & MIS (ICEMIS), pp. 1–6, doi: 10.1109/ICEMIS.2016.7745306.
[28] Davidovic, B. and Labus, A., (2016). A smart home system based on sensor technology, Facta Univ. Ser. Electron. Energetics, 29, 451–460.
[29] Jabbar, W.A., et al., (2019). Design and Fabrication of Smart Home with Internet of Things Enabled Automation System, IEEE Access, 7, 144059–144074.
[30] Bhatt, A. and Patoliya, J., (2016). Cost effective digitization of home appliances for home automation with low-power WiFi devices, International Conference on Advances in Electrical, Electronics, Information, Communication and Bio-Informatics (AEEICB), pp. 643–648, Chennai, India.
[31] Yan, W., et al., (2019). Smart home implementation based on Internet and WiFi technology, Chinese Control Conference (CCC), pp. 9072–9077, Hangzhou, China.
[32] Joshi1, M., and Kumbhare, K., (2018). A Review on Efficient Mac Layer Handoff Protocol to Reduce Handoff Latency for Wi-Fi Based Wireless Network, International Journal of Scientific Research in Computer Science and Engineering, Vol. 6, Issue.2, pp. 82–86.
[33] Sebastian, A. and Sivagurunathan, S., (2018). A Survey on Load Balancing Schemes in RPL based Internet of Things, International Journal of Scientific Research in Network Security and Communication, Vol. 6, Issue 3, pp. 43–49.
[34] Jabbar, W. A., et al., (2018). Design and Implementation of IoT-Based Automation System for Smart Home, International Symposium on Networks, Computers and Communications (ISNCC), pp. 1–6, Italy.
[35] Bhatt, P., Thaker, B., and Shah, N., (2018). A Survey on Developing Secure IoT Products”, International Journal of Scientific Research in Computer Science and Engineering, Vol. 6, Issue 5, pp. 41–44.
[36] Singh, U., and Ansari, M.A. (2019). Smart Home Automation System Using Internet of Things, 2nd International Conference on Power Energy, Environment and Intelligent Control (PEEIC), 144–149.
[37] Kodali, R.K., et al., (2016). IoT based smart security and home automation system, International Conference on Computing, Communication and Automation (ICCCA), pp. 1286–1289, Noida, India.
[38] Majeed, R., et al., (2020). An Intelligent, Secure, and Smart Home Automation System, 1058-9244, volume 2020, Article ID 4579291, Scientific Programming, Hindawi, https://doi.org/10.1155/2020/4579291.
[39] Rathnayake, K. A. S. V., et al., (2016). Voice operated home automation system based on Kinect sensor, IEEE International Conference on Information and Automation for Sustainability (ICIAfS), pp. 1–5, Sri Lanka.
[40] Venkatraman, S., and Overmars, A., and Thong, M., (2021). Smart Home Automation—Use Cases of a Secure and Integrated Voice-Control System. Systems, 9(4), 77. https://doi.org/10.3390/systems9040077.
[41] Uma, S., et al., (2019). IoT based Voice/Text Controlled Home Appliances, Procedia Computer Science, Volume 165, Pages 232–238, ISSN 1877-0509, https://doi.org/10.1016/j.procs.2020.01.085.
[42] Yang. C., (2021). Design of Smart Home Control System Based on Wireless Voice Sensor, Journal of Sensors, Hindawi, Article ID 8254478, Vol. 2021, https://doi.org/10.1155/2021/8254478.
[43] Mittal, Y., et al., (2015). A voice-controlled multi-functional Smart Home Automation System, Annual IEEE India Conference (INDICON), pp. 1–6, doi: 10.1109/INDICON.2015.7443538.
[44] Erić, T., et al., (2017). Voice control for smart home automation: Evaluation of approaches and possible architectures, IEEE 7th International Conference on Consumer Electronics – Berlin (ICCE-Berlin), pp. 140–142, doi: 10.1109/ICCE-Berlin.2017.8210613.
[45] Celebre, A. M. D., et al., (2015). Home automation using raspberry Pi through Siri enabled mobile devices, International Conference on Humanoid, Nanotechnology, Information Technology, Communication and Control, Environment and Management (HNICEM), pp. 1–6, doi: 10.1109/HNICEM.2015.7393270.
[46] Piyare. R., and Tazil, M. (2011). Bluetooth based Home Automation System using Cell Phone, IEEE 15th International Symposium on Consumer Electronics (ISCE), 192–195.
[47] Alshu’Eili, H., Gupta, G. S., and Mukhopadhyay, S., (2011). Voice recognition based wireless home automation system. In 4th International Conference on Mechatronics: Integrated Engineering for Industrial and Societal Development, ICOM’11 – Conference Proceedings Institute of Electrical and Electronics Engineers (IEEE), https://doi.org/10.1109/ICOM.2011.5937116.
[48] Hidayat, S., and Firmanda, S. F., (2015). Scheduler and voice recognition on home automation control system, 3rd International Conference on Information and Communication Technology (ICoICT), pp. 150–155, doi: 10.1109/ICoICT.2015.7231413.
[49] Jain, S., Vaibhav, A., and Goyal, L., (2014). Raspberry Pi based interactive home automation system through E-mail, International Conference on Reliability Optimization and Information Technology (ICROIT), pp. 277–280, doi: 10.1109/ICROIT.2014.6798330.
[50] Narender, M., and Vijaylakshmi, M., (2014). Raspberry Pi based Advanced Scheduled Home Automation System through E-mail, IEEE International Conference on Computational Intelligence and Computing Research, pp. 1–4, doi: 10.1109/ICCIC.2014.7238413.
[51] Pavithra, D., and Balakrishnan, R., (2015). IoT based Monitoring and Control System for Home Automation, Global Conference on Communication Technologies (GCCT), pp. 169–173, 2015, doi: 10.1109/GCCT.2015.7342646.
[52] Alsuhaym, F. et al., (2021). Toward Home Automation: An IoT Based Home Automation System Control and Security, International Congress of Advanced Technology and Engineering (ICOTEN), pp. 1–11, doi: 10.1109/ICOTEN52080.2021.9493464.
[53] Purwar, K., and Verma, A., (2017). Smart Home Automation System based on IoT through Speech, International Journal of Computer Applications, 172, 36–42.
[54] Haque, M. E., et al. (2019). IoT Based Home Automation System with Customizable GUI and Low Cost Embedded System, International Conference on Sustainable Technologies for Industry 4.0 (STI), pp. 1–5, doi: 10.1109/STI47673.2019.9068035.
[55] Kumar, K. P. M., et al. (2019). Intrusion detection system based on GA-fuzzy classifier for detecting malicious attacks, Concurrency and Computation Practice and Experience 33(1), https://doi.org/10.1002/cpe.5242.
[56] Asaithambi, S.P.R., Venkatraman, S., and Venkatraman. R., (2021). Big Data and Personalisation for Non-Intrusive Smart Home Automation, Big Data and Cognitive Computing. 5(1):6, https://doi.org/10.3390/bdcc5010006.
[57] Anathi, M., and Vijayakumar, K., (2020). An Intelligent Approach for Dynamic Network Traffic Restriction using MAC Address Verification, Computer Communications, Volume 154, pp. 559–564, ISSN 0140-3664, https://doi.org/10.1016/j.comcom.2020.02.021.
[58] Kumar, K., (2017). Fog computing: The essential catalyst for optimizing the true potential of cloud-based internet of things, International Journal of Applied Research on Information Technology and Computing, 8(3), 247–262, ISSN: 2249-3212, DOI: 10.5958/0975-8089.2017.00021.5.
Biographies

Santosh Kumar Sahoo is currently working as Associate Professor in the Department of Electronics & Instrumentation Engineering at CVR College of Engineering, Hyderabad, India. He has 16 years of teaching experience including 5 years of research experience. He has published 30 research publications in international journals, 45 papers in the proceedings of refereed international and national conferences with 5 best paper awards. He has reviewed more than 100 technical papers, served as reviewer and editorial board member for more than 20 journals and published 2 books in repute international publishers. He has served roughly 25 conference and workshops. He has delivered invited lectures, Keynote addresses and Chaired technical sessions in various international conferences. He has received Out Standing Teacher Award by Indo Global Chamber of Commerce-2018. He is an active member in IEEE, life member in ISTE, IETE etc.

Sushant Kumar Pattnaik received his M. Tech degree in Electronics and Communication from NIT, Rourkela in 2010. He received his B. E. (Electrical and Electronics Engineering) from Berhampur University in 2001. He is now working as Assistant Professor, Electronics & Communication Engineering, Silicon Institute of Technology, Bhubaneswar. He has got more than 11 years teaching and research experience in the field of VLSI Design, IoT & Embedded Systems. He was having 3 years of Industrial Experience in the field of power electronics (UPS Manufacturing Company) and 3 years of Research experience in the field of VLSI & Embedded Systems at NIT Rourkela.

Soumya Ranjan Samal received his Ph.D. degree in Communication Networks, Faculty of Telecommunications from Technical University of Sofia at Sofia, Bulgaria. He received his B.Tech. degree in Electronics & Instrumentation Engineering from Biju Patnaik University of Technology, Bhubaneswar, India in 2004. Soumya then went on to pursue his M.E. in Computer Science & Engineering from the Utkal University of Bhubaneswar, India in 2009. He, as a Senior Assistant Professor in Silicon Institute of Technology, Bhubaneswar, India has acquired a solid experience about 15 years of teaching in Communication Engineering. Soumya also worked as a Project Engineer in Indian Institute of Technology, Bombay, India in 2005. His research area of interest includes, Interference Management in 6G cellular network, Green Communication movement to develop Energy Efficient solutions through antenna parameters and IoT.

Chinmaya Kumar Nayak is currently working as a Sr. Assistant Professor in Faculty of Emerging Technologies (FET) – Sri Sri University, Odisha, India. He is having 15 years of reach experience in teaching. He received his Ph.D. (Computer Science and Engineering) from Veer Surendra Sai University of Technology (VSSUT), Burla, Odisha,India. He received his B.Tech(Information Technology) and M.Tech (Computer Science and Engineering) from Biju Patnaik University of Technology, Odisha, India. His research interest includes Computer Networks, Wireless Sensor Networks, Data Science, Artificial Intelligence and Machine Learning.

Jitendra Kumar Das has received his Ph. D. degree in Electronics and Communication from NIT, Rourkela in 2011. He received his B. E. (Electronics and Telecommunication) from Utkal University in 1992. He received his M. Tech in EE (Electronics System and Communication) from NIT, Rourkela in 2004. He is now working as Associate Professor, School of Electronics Engineering, KIIT Deemed to be University, Bhubaneswar. He successfully guided 3 Ph. D. student and 20 MTECH students. He has got more than 15 years teaching experience in the field of VLSI Design, Embedded Systems and Signal Processing. His research interest are Semiconductor Device and Nanostructures, VLSI DSP, Embedded System Design and IoT, FPGA and Reconfigurable computing.

Vladimir Poulkov has received the M.Sc. and Ph.D. degrees from the Technical University of Sofia, Sofia, Bulgaria. He has more than 30 years of teaching, research, and industrial experience in the field of telecommunications, as a Research and Development Engineer in industry, and has been a Full Professor with the Faculty of Telecommunications, Technical University of Sofia, since 1981. He has successfully managed and realized numerous industrial and engineering projects, related to the development of the transmission and access network infrastructures in Bulgaria, many Research and Development and educational projects. He was the Dean of the Faculty of the Telecommunications from 2007 to 2015. He is currently the Head of the Teleinfrastructure Research and Development Laboratory with the Technical University of Sofia, and the Chairman of the Bulgarian Cluster of Telecommunications, Sofia, Senior IEEE Member and co-founder of the CONASENSE (Communication, Navigation, Sensing and Services) society. He has authored more than 100 scientific publications and is tutoring B.Sc., M.Sc., and Ph.D. courses in Information Transmission Theory and Next Generation Access Networks. His current research interests include interference and resource management in next-generation network and Internet of Things.
Journal of Mobile Multimedia, Vol. 18_6, 1471–1496.
doi: 10.13052/jmm1550-4646.1861
© 2022 River Publishers